Malware analysis Malicious activity
Por um escritor misterioso
Last updated 31 março 2025
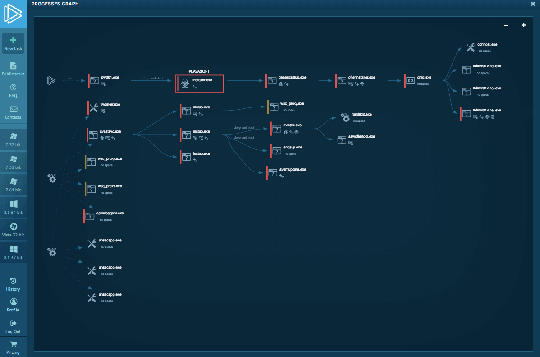
Interactive Online Malware Sandbox

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Detail procedure of malware analysis

AlienVault - Open Threat Exchange

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks

Cybersecurity Search Engine

Malware analysis lockysample.bin.zip Malicious activity
TryHackMe Hacktivities

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Malware analysis mykey_.rar Malicious activity
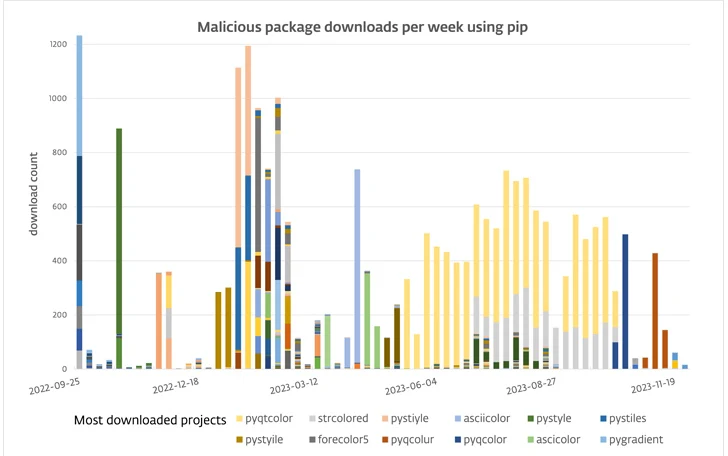
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus
Recomendado para você
-
 Setup OrthoInTouch with topsOrtho - OrthoInTouch - Appointment Reminders31 março 2025
Setup OrthoInTouch with topsOrtho - OrthoInTouch - Appointment Reminders31 março 2025 -
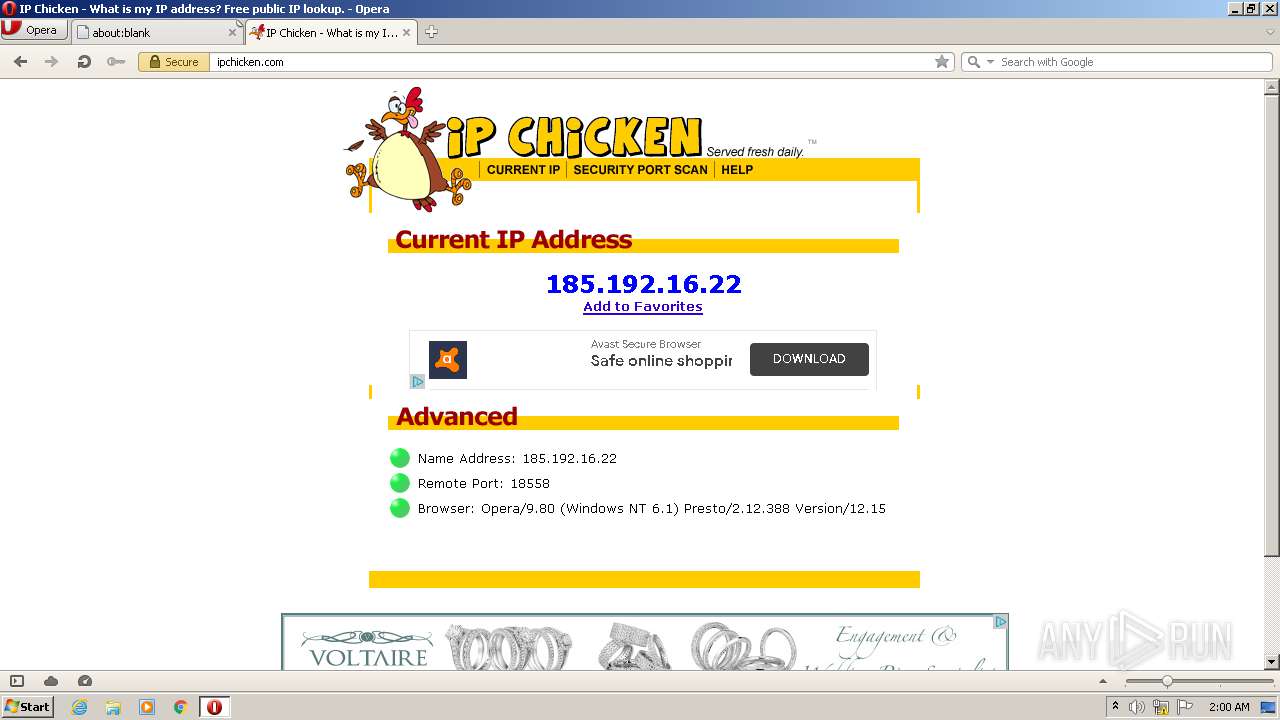
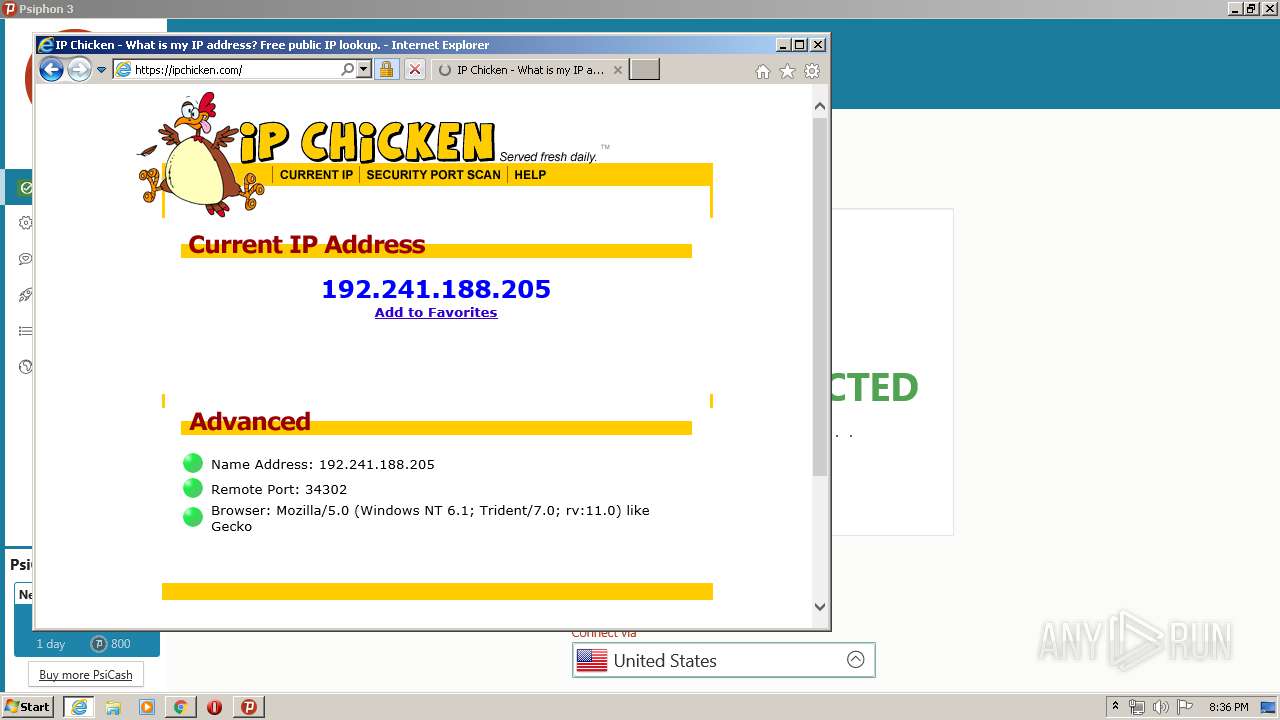
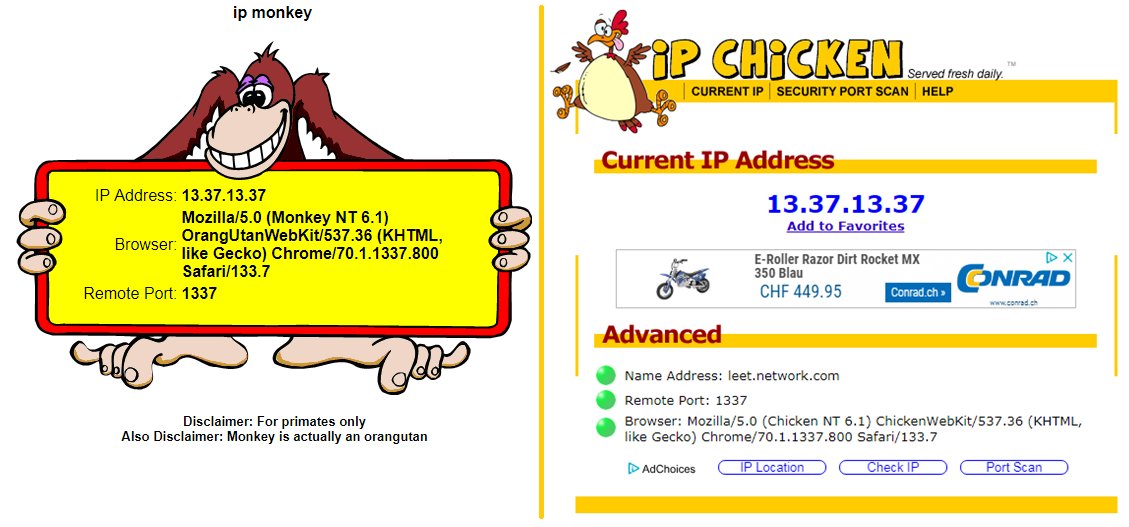 Pascal Gujer on X: / : not only showing your remote IP but also your remote port #ipchicken #ipmonkey #identification deanonymize within carrier-grade natted networks :sigh: / X31 março 2025
Pascal Gujer on X: / : not only showing your remote IP but also your remote port #ipchicken #ipmonkey #identification deanonymize within carrier-grade natted networks :sigh: / X31 março 2025 -
 Malware analysis Suspicious activity31 março 2025
Malware analysis Suspicious activity31 março 2025 -
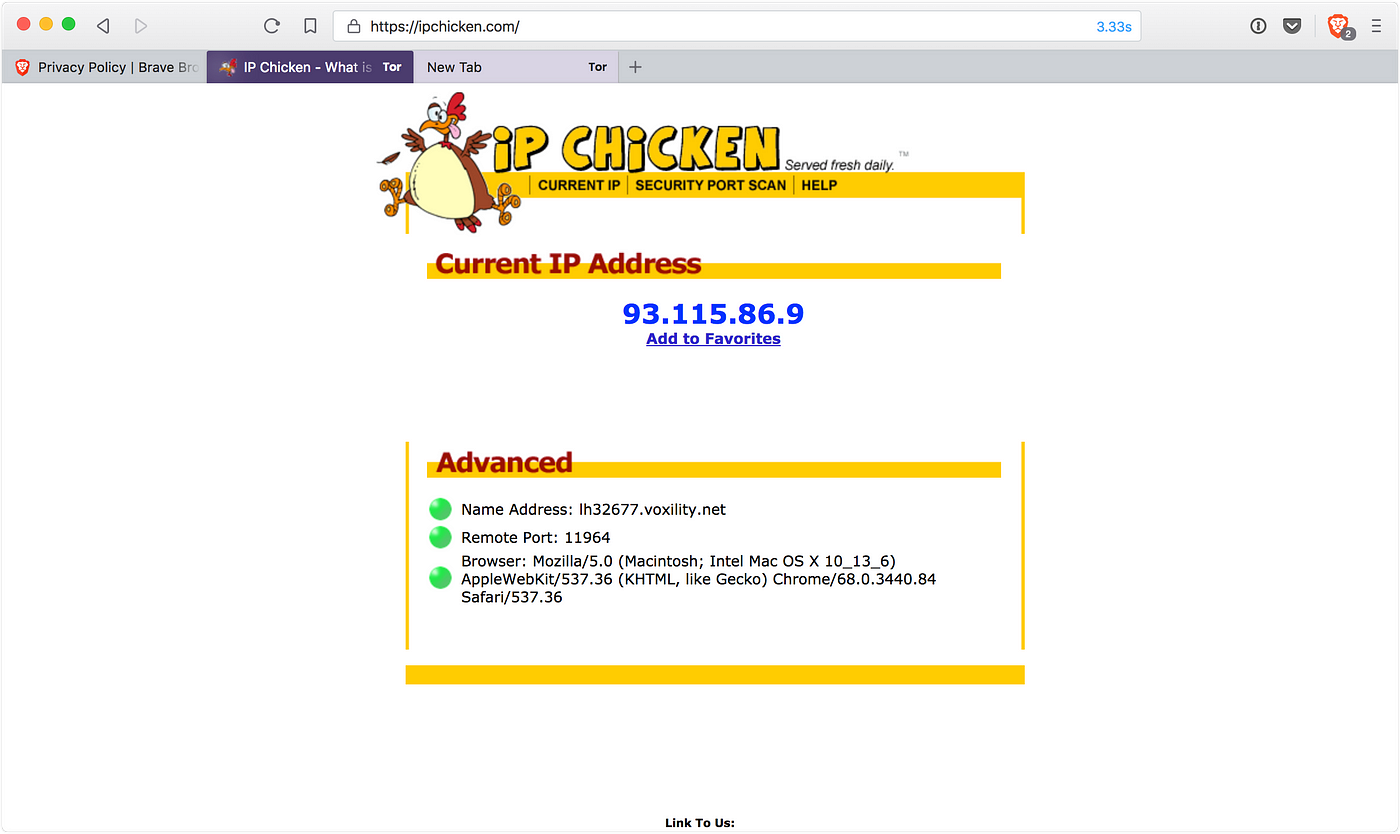 Using a truly private browser — Brave, by Dave Smith31 março 2025
Using a truly private browser — Brave, by Dave Smith31 março 2025 -
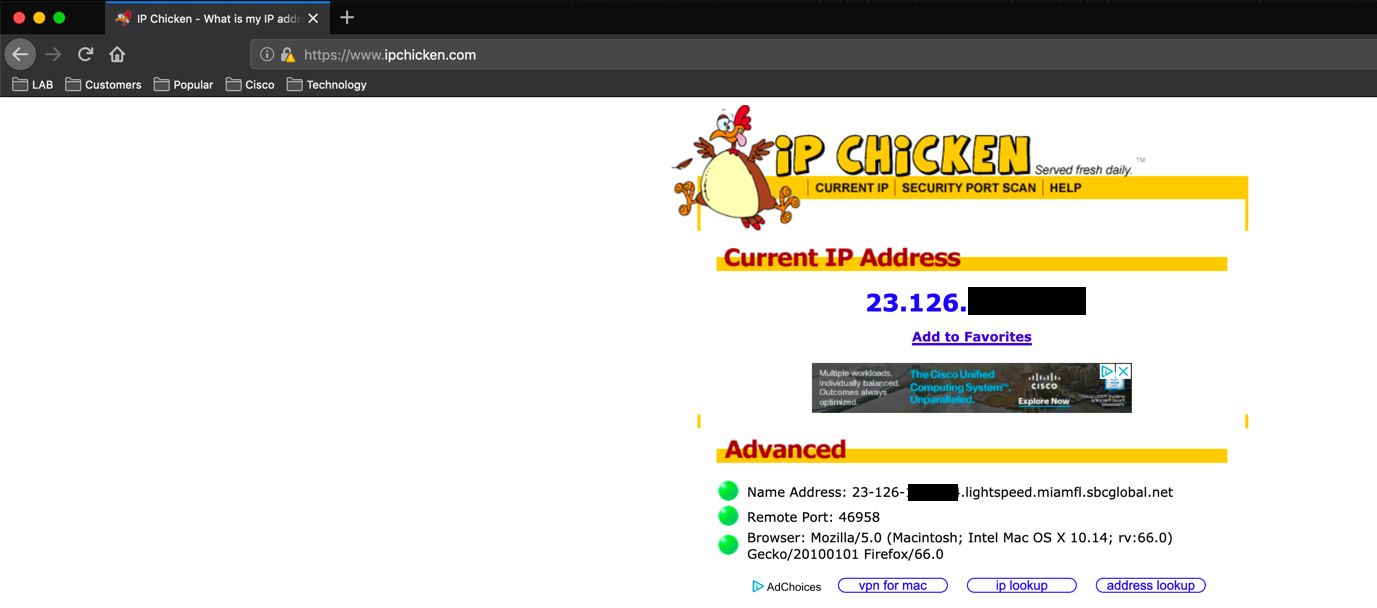
 8 Sites That Show Your IP Address –31 março 2025
8 Sites That Show Your IP Address –31 março 2025 -
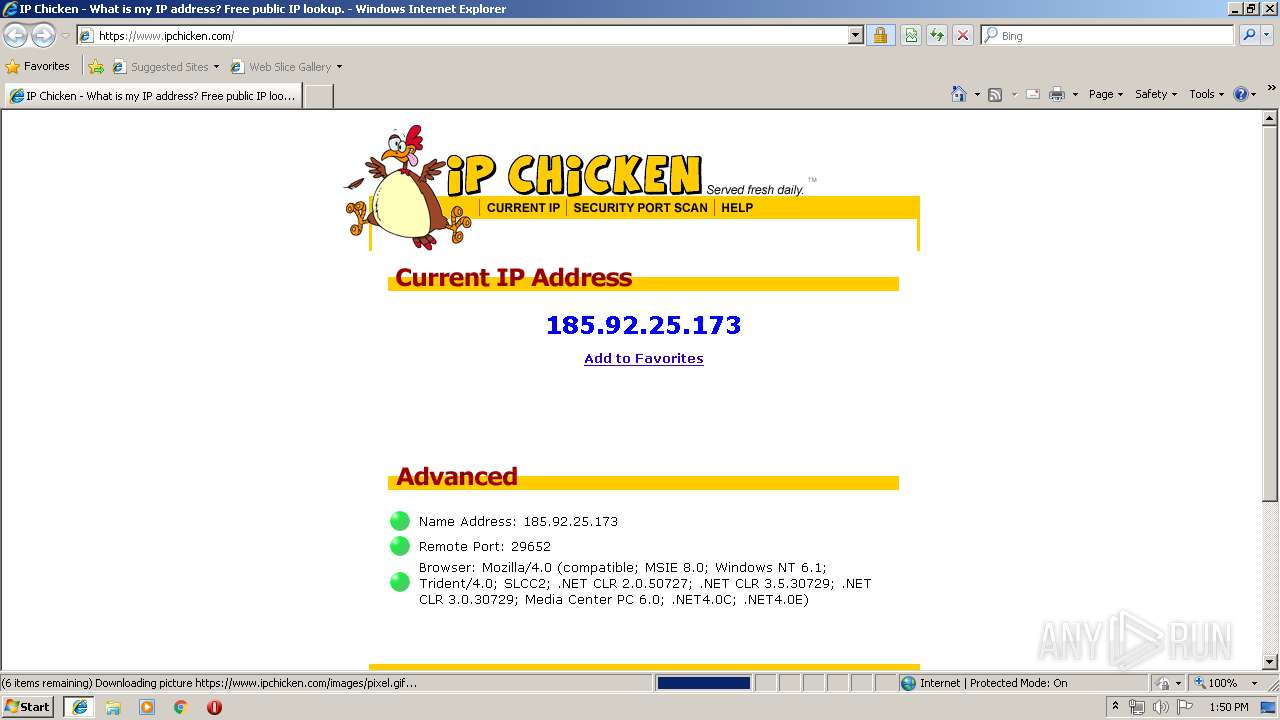
 Troubleshooting NAT on Fortigate Firewall – InfoSec Monkey31 março 2025
Troubleshooting NAT on Fortigate Firewall – InfoSec Monkey31 março 2025 -
 What is Tor Browser & How to Setup Tor31 março 2025
What is Tor Browser & How to Setup Tor31 março 2025 -
 IP Address Sweep and Port Scan, Junos OS31 março 2025
IP Address Sweep and Port Scan, Junos OS31 março 2025 -
 Malware analysis Malicious activity31 março 2025
Malware analysis Malicious activity31 março 2025 -
 Hacking Package Pickup31 março 2025
Hacking Package Pickup31 março 2025
você pode gostar
-
 Anime fan art characters on Behance31 março 2025
Anime fan art characters on Behance31 março 2025 -
El Calvo de Minecraft - Calvos, ya tenemos discord oficial. Al igual que el grupo, servirá como comunidad para poder interactuar, compartir memes y poder jugar. Son todos invitados a formar parte.31 março 2025
-
 2021/22 Bundesliga Championship Medal Germany Bundesliga31 março 2025
2021/22 Bundesliga Championship Medal Germany Bundesliga31 março 2025 -
Warriors the movie 猫武士电影31 março 2025
-
 Construtor de Sites da HostCuritiba (41) 3285-504531 março 2025
Construtor de Sites da HostCuritiba (41) 3285-504531 março 2025 -
 REVIEW: The Last Kingdom Season 2 - Grimdark Magazine31 março 2025
REVIEW: The Last Kingdom Season 2 - Grimdark Magazine31 março 2025 -
 Sombras da Guerra” revela Mordor em toda a sua grandeza31 março 2025
Sombras da Guerra” revela Mordor em toda a sua grandeza31 março 2025 -
 Legging Fitness Infantil Memories em Poliamida Preta31 março 2025
Legging Fitness Infantil Memories em Poliamida Preta31 março 2025 -
 doando contas roblox entrem no grupo|Pesquisa do TikTok31 março 2025
doando contas roblox entrem no grupo|Pesquisa do TikTok31 março 2025 -
 Bandai shf ranking de reis figuras anime bojji kage ativo conjunto boneca figura de ação coleção decoração modelo brinquedo presentes natal - AliExpress31 março 2025
Bandai shf ranking de reis figuras anime bojji kage ativo conjunto boneca figura de ação coleção decoração modelo brinquedo presentes natal - AliExpress31 março 2025

