PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 27 março 2025
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
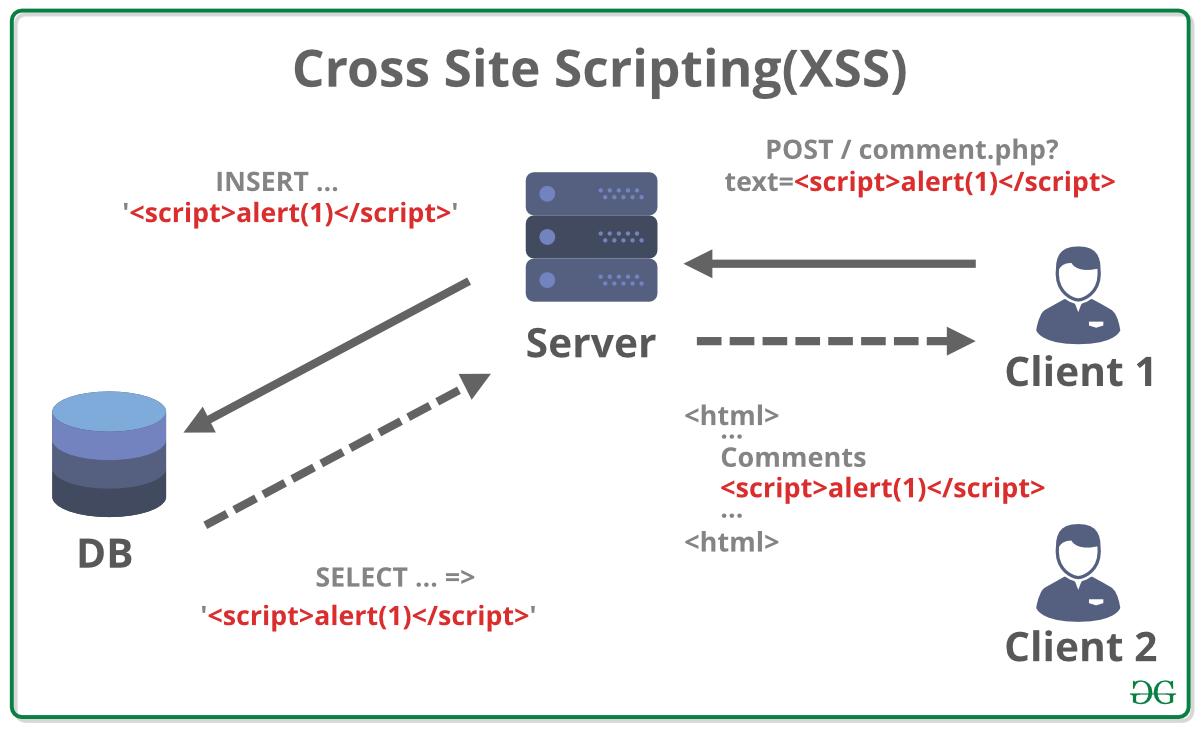
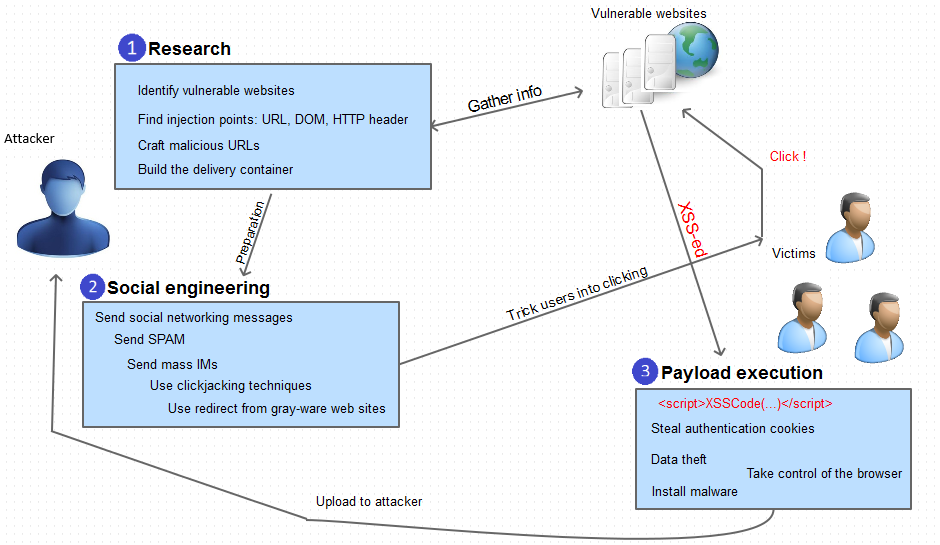
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://ars.els-cdn.com/content/image/1-s2.0-S2590123023003936-gr1.jpg)
Cost-effective detection system of cross-site scripting attacks using hybrid learning approach - ScienceDirect
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.vaadata.com/blog/wp-content/uploads/2022/09/Reflected-XSS-attack-1024x535.jpg)
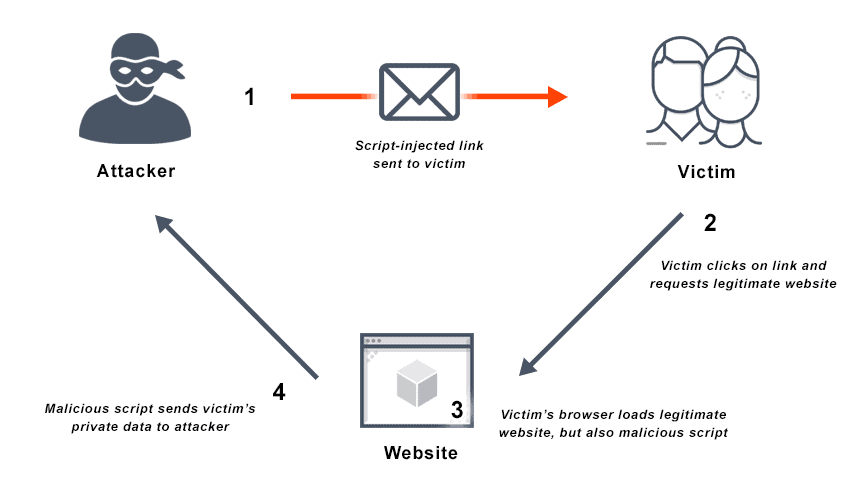
XSS: Principles, Attacks and Security Best Practices
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.mdpi.com/futureinternet/futureinternet-11-00177/article_deploy/html/images/futureinternet-11-00177-g001.png)
Future Internet, Free Full-Text
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://cdn.acunetix.com/wp_content/uploads/2010/09/sql_inj_xss.gif)
SQL Injection - MDN Web Docs Glossary: Definitions of Web-related terms
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/lw685/springer-static/image/art%3A10.1007%2Fs10462-023-10433-3/MediaObjects/10462_2023_10433_Fig12_HTML.png)
Detection of cross-site scripting (XSS) attacks using machine learning techniques: a review
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://miro.medium.com/v2/resize:fit:712/1*Gr8Sw8nEpV8SKMz8rBRL_A.jpeg)
Remote MS Office template injection, by Tho Le
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://0.academia-photos.com/attachment_thumbnails/67471425/mini_magick20210531-27012-1mvlz8r.png?1622447148)
PDF) Exploitation of Cross-Site Scripting (XSS) Vulnerability on Real World Web Applications and its Defense
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://miro.medium.com/v2/resize:fit:1400/1*OxkBOt9qymWtNpds8CZy7g.png)
4 IFrame Security Concerns You Should Know, by Piumi Liyana Gunawardhana
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/Jai-Puneet-Singh/publication/302893095/figure/fig4/AS:360404925599752@1462938638758/SQL-Injection-attack-using-the-XSS_Q320.jpg)
SQL Injection attack using the XSS
Recomendado para você
-
 Cross Site Scripting (XSS) - Payload Generator27 março 2025
Cross Site Scripting (XSS) - Payload Generator27 março 2025 -
 What is Cross Site Scripting (XSS) ? - GeeksforGeeks27 março 2025
What is Cross Site Scripting (XSS) ? - GeeksforGeeks27 março 2025 -
What is cross-site scripting (XSS)?, Tutorial & examples27 março 2025
-
 What is Cross Site Scripting? Definition & FAQs27 março 2025
What is Cross Site Scripting? Definition & FAQs27 março 2025 -
 XSS: Principles, Attacks and Security Best Practices27 março 2025
XSS: Principles, Attacks and Security Best Practices27 março 2025 -
 Cross Site Scripting -XSS🌐. 🌐What is Cross-Site Scripting (XSS27 março 2025
Cross Site Scripting -XSS🌐. 🌐What is Cross-Site Scripting (XSS27 março 2025 -
 SQL injection and XSS: what white hat hackers know about trusting27 março 2025
SQL injection and XSS: what white hat hackers know about trusting27 março 2025 -
 How DOM Based XSS Attacks work27 março 2025
How DOM Based XSS Attacks work27 março 2025 -
 Understanding Cross-Site Scripting Attacks27 março 2025
Understanding Cross-Site Scripting Attacks27 março 2025 -
 SQL Injection attack using the XSS27 março 2025
SQL Injection attack using the XSS27 março 2025
você pode gostar
-
 Read Bokura Wa Minna Kawaisou Vol.1 Chapter 24 on Mangakakalot27 março 2025
Read Bokura Wa Minna Kawaisou Vol.1 Chapter 24 on Mangakakalot27 março 2025 -
 Live Wire (Motley Crue) by N. Sixx27 março 2025
Live Wire (Motley Crue) by N. Sixx27 março 2025 -
 Roblox logo and symbol, meaning, history, PNG27 março 2025
Roblox logo and symbol, meaning, history, PNG27 março 2025 -
 CSGO 2 LANÇAMENTO OFICIAL MEU PC NÃO RODA CS 227 março 2025
CSGO 2 LANÇAMENTO OFICIAL MEU PC NÃO RODA CS 227 março 2025 -
 Google Chrome: conoce el 'truco' para cambiar al dinosaurio T-Rex por Super Mario Bros, Fotos, Video, Tecnología27 março 2025
Google Chrome: conoce el 'truco' para cambiar al dinosaurio T-Rex por Super Mario Bros, Fotos, Video, Tecnología27 março 2025 -
 9 Best Opening Lines for Public Speaking27 março 2025
9 Best Opening Lines for Public Speaking27 março 2025 -
 Carro 5 Speed Gear Stick Shift Knob Head para Peugeot 106 107 205 20627 março 2025
Carro 5 Speed Gear Stick Shift Knob Head para Peugeot 106 107 205 20627 março 2025 -
 Pokémon HeartGold Nuzlocke but ONLY Johto Pokémon!27 março 2025
Pokémon HeartGold Nuzlocke but ONLY Johto Pokémon!27 março 2025 -
 Roblox Jacket27 março 2025
Roblox Jacket27 março 2025 -
 Avicii - Free feat. Wayne Hector (Unreleased)27 março 2025
Avicii - Free feat. Wayne Hector (Unreleased)27 março 2025
