How hackers use idle scans in port scan attacks
Por um escritor misterioso
Last updated 26 março 2025
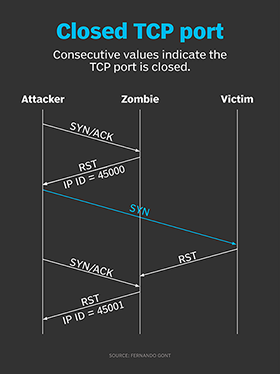
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.

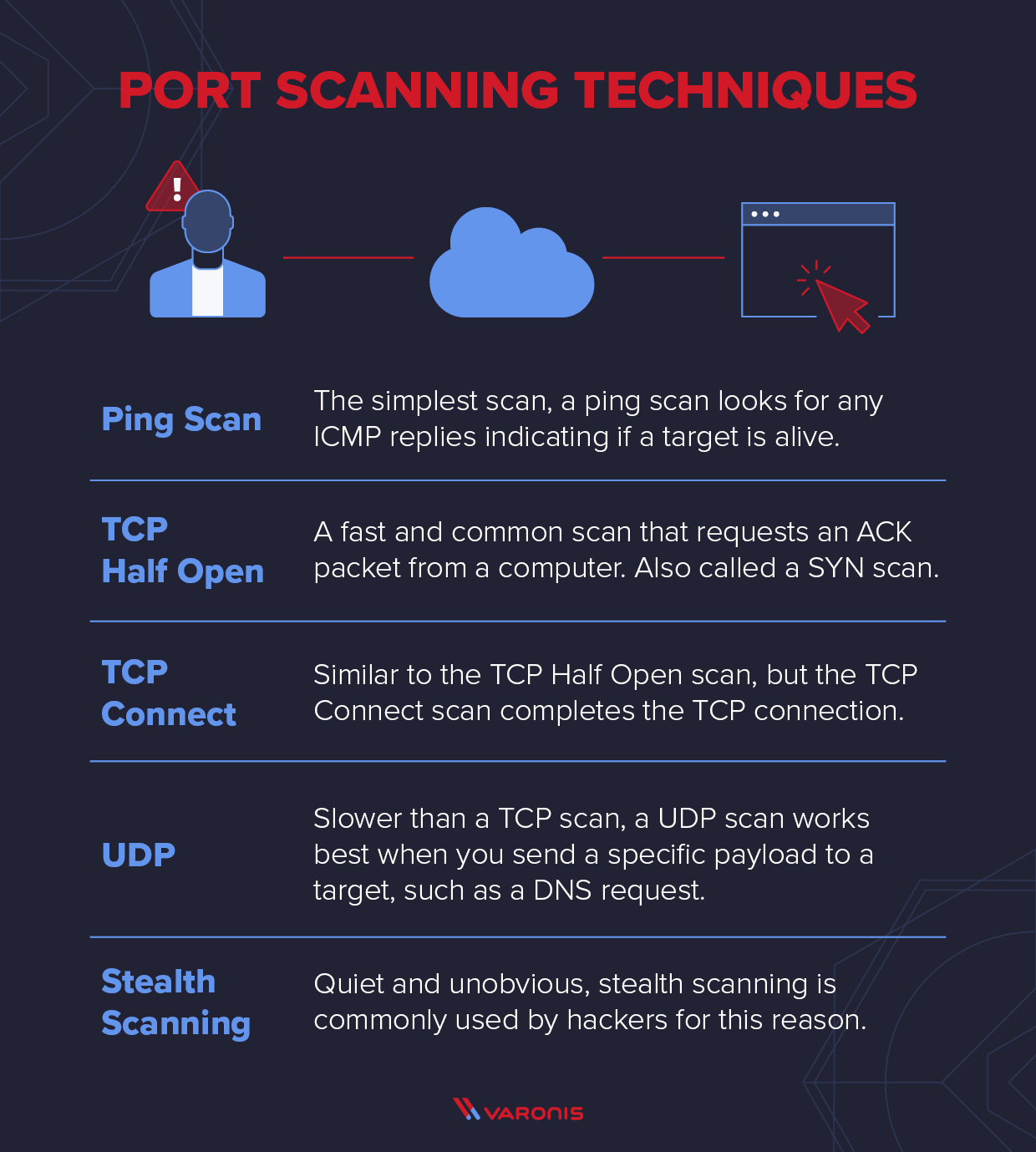
Port Scanning: A Comprehensive Guide for Safeguarding Cyberspace
What is a Cyber Attack? Definition and Related FAQs
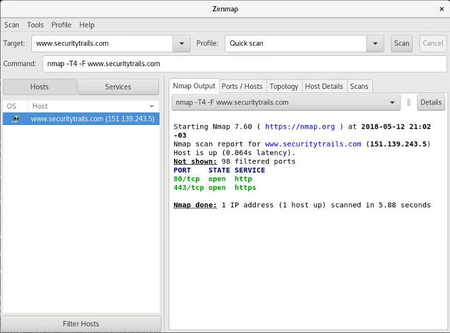
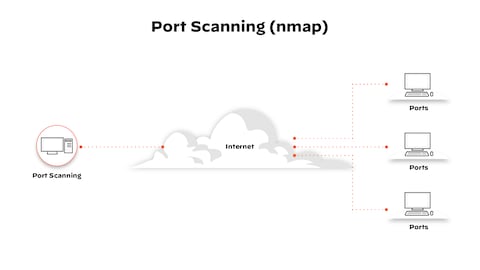
What Is Nmap? A Comprehensive Tutorial For Network Mapping
PPT - Port Scanning PowerPoint Presentation, free download - ID:4633948
Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan

What Is an Idle Scan? (with pictures)

Hack Like a Pro: Advanced Nmap for Reconnaissance « Null Byte :: WonderHowTo

What is Idle Scan? ICterra Information and Communication Technologies

What is Idle Scan? ICterra Information and Communication Technologies

Legal Issues Nmap Network Scanning

Port Scanning: A Comprehensive Guide for Safeguarding Cyberspace
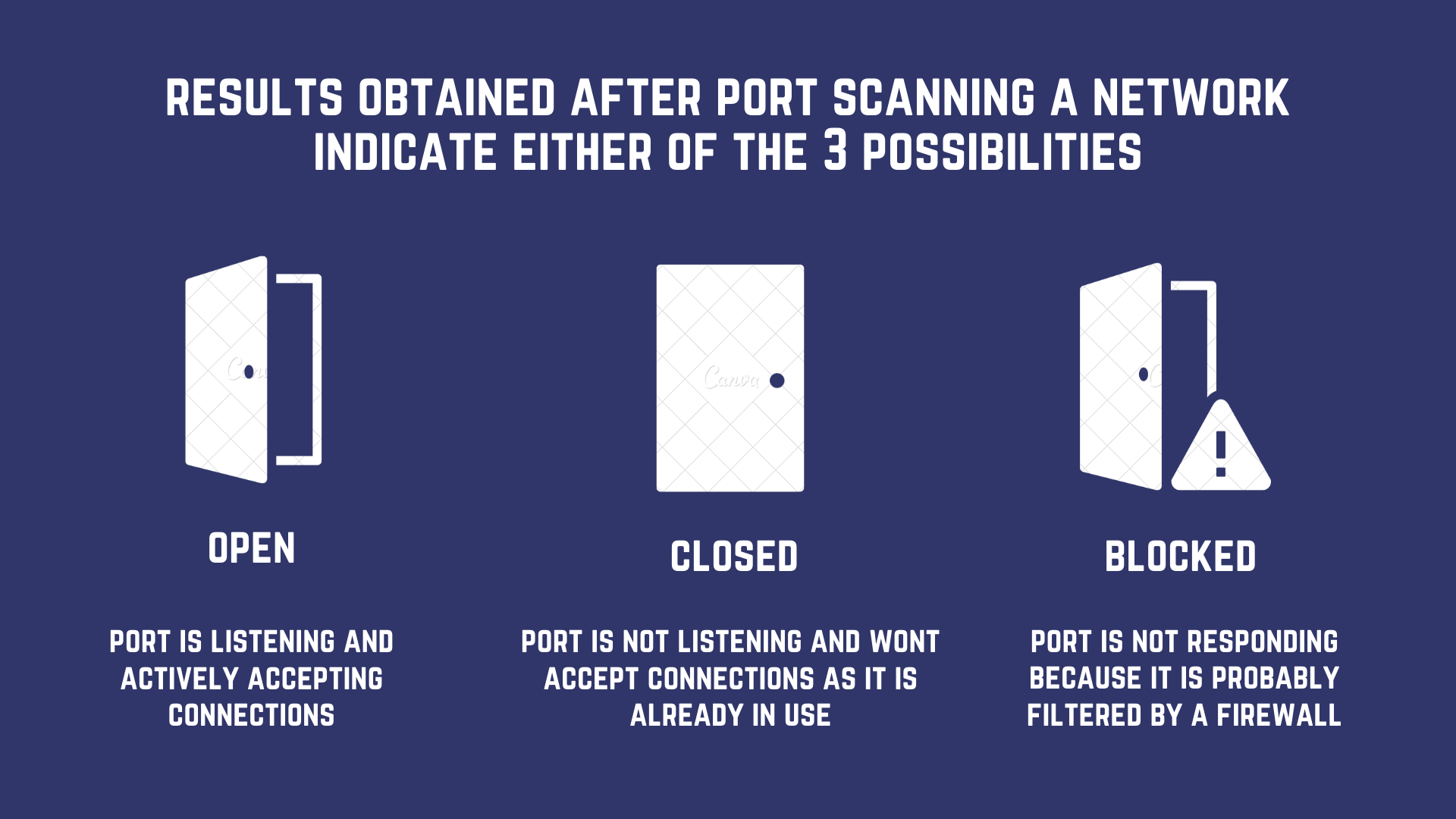
Port Scanning based Attacks
Recomendado para você
-
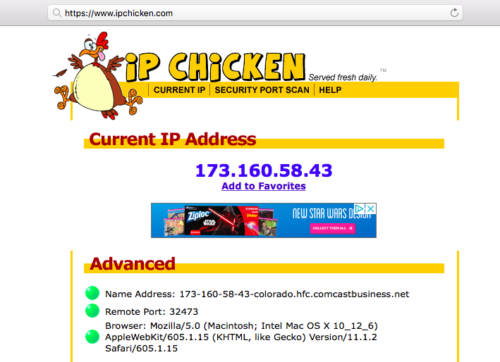
 How to extract your outside IP address - What's My IP - IP Chicken - IP Monkey26 março 2025
How to extract your outside IP address - What's My IP - IP Chicken - IP Monkey26 março 2025 -
 Away Viewing Fix - Dynamic URL Change, WiFi Baby, Compare Baby Monitors 201926 março 2025
Away Viewing Fix - Dynamic URL Change, WiFi Baby, Compare Baby Monitors 201926 março 2025 -
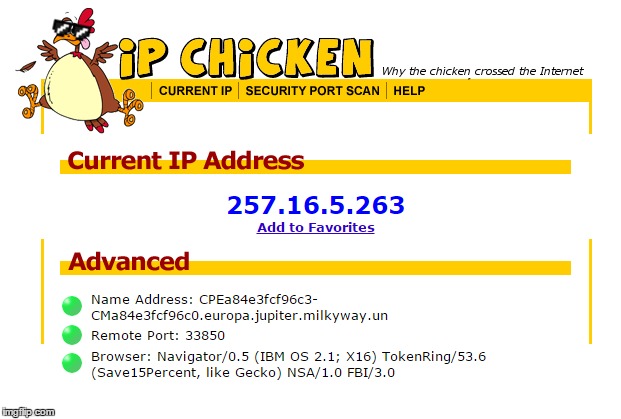 chicken Memes & GIFs - Imgflip26 março 2025
chicken Memes & GIFs - Imgflip26 março 2025 -
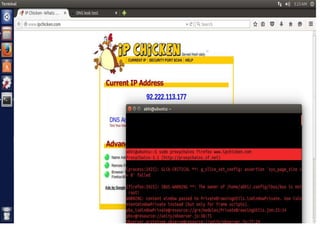 Anonymous Security Scanning and Browsing26 março 2025
Anonymous Security Scanning and Browsing26 março 2025 -
 Explaining Port Scanning. A port scan is a common technique…, by Arth Awasthi26 março 2025
Explaining Port Scanning. A port scan is a common technique…, by Arth Awasthi26 março 2025 -
 Top 5 Most Popular Port Scanners in CyberSecurity26 março 2025
Top 5 Most Popular Port Scanners in CyberSecurity26 março 2025 -
 What is a Port Scan? - Palo Alto Networks26 março 2025
What is a Port Scan? - Palo Alto Networks26 março 2025 -
Ethical Hacking With Net26 março 2025
-
 Alt using troll awareness meme - Imgflip26 março 2025
Alt using troll awareness meme - Imgflip26 março 2025 -
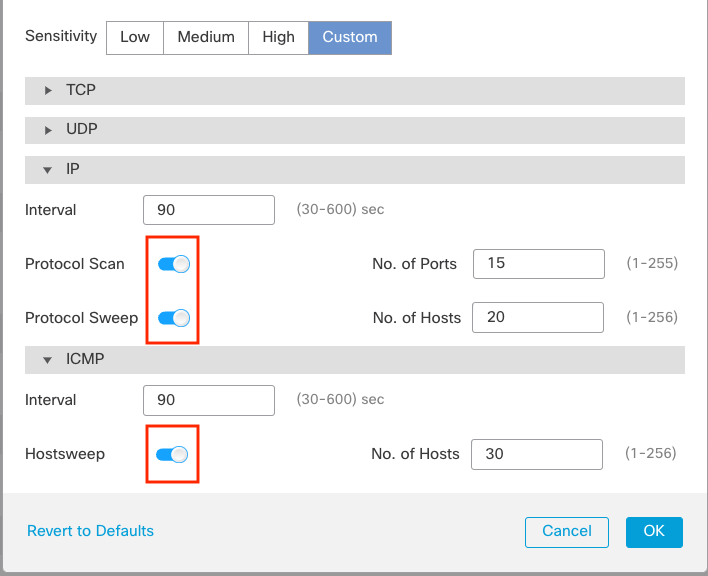 Port Scan Detection26 março 2025
Port Scan Detection26 março 2025
você pode gostar
-
 Jogo Futebol Botão26 março 2025
Jogo Futebol Botão26 março 2025 -
 Paraguai elimina Portugal nos 'quartos' da Copa das Nações26 março 2025
Paraguai elimina Portugal nos 'quartos' da Copa das Nações26 março 2025 -
 Forever 21 reportedly closing 100 stores on restructure26 março 2025
Forever 21 reportedly closing 100 stores on restructure26 março 2025 -
 Cruzeiro x Flamengo, AO VIVO, com a Voz do Esporte, às 17h3026 março 2025
Cruzeiro x Flamengo, AO VIVO, com a Voz do Esporte, às 17h3026 março 2025 -
 Dio Brando - Ariyon Scythe - Digital Art, People & Figures26 março 2025
Dio Brando - Ariyon Scythe - Digital Art, People & Figures26 março 2025 -
 BMW G 310 RR: conheça a nova moto esportiva 'popular' da marca26 março 2025
BMW G 310 RR: conheça a nova moto esportiva 'popular' da marca26 março 2025 -
 Chrono Cross: The Radical Dreamers Edition26 março 2025
Chrono Cross: The Radical Dreamers Edition26 março 2025 -
 Colégio Objetivo DF realiza 1º Festival Interno de Xadrez - Jornal de Brasília26 março 2025
Colégio Objetivo DF realiza 1º Festival Interno de Xadrez - Jornal de Brasília26 março 2025 -
 Cut the Rope 2 Level 6726 março 2025
Cut the Rope 2 Level 6726 março 2025 -
 Mundial de Clubes 2021: Conmebol discute os critérios de classificação26 março 2025
Mundial de Clubes 2021: Conmebol discute os critérios de classificação26 março 2025
