DigitalResidue's Forensics: Malware Incident Response pt. 2. (Collecting Volatile and Non-Volatile data)
Por um escritor misterioso
Last updated 26 março 2025
DigitalResidue's Forensics: Malware Incident Response pt. 2. (Collecting Volatile and Non-Volatile data)
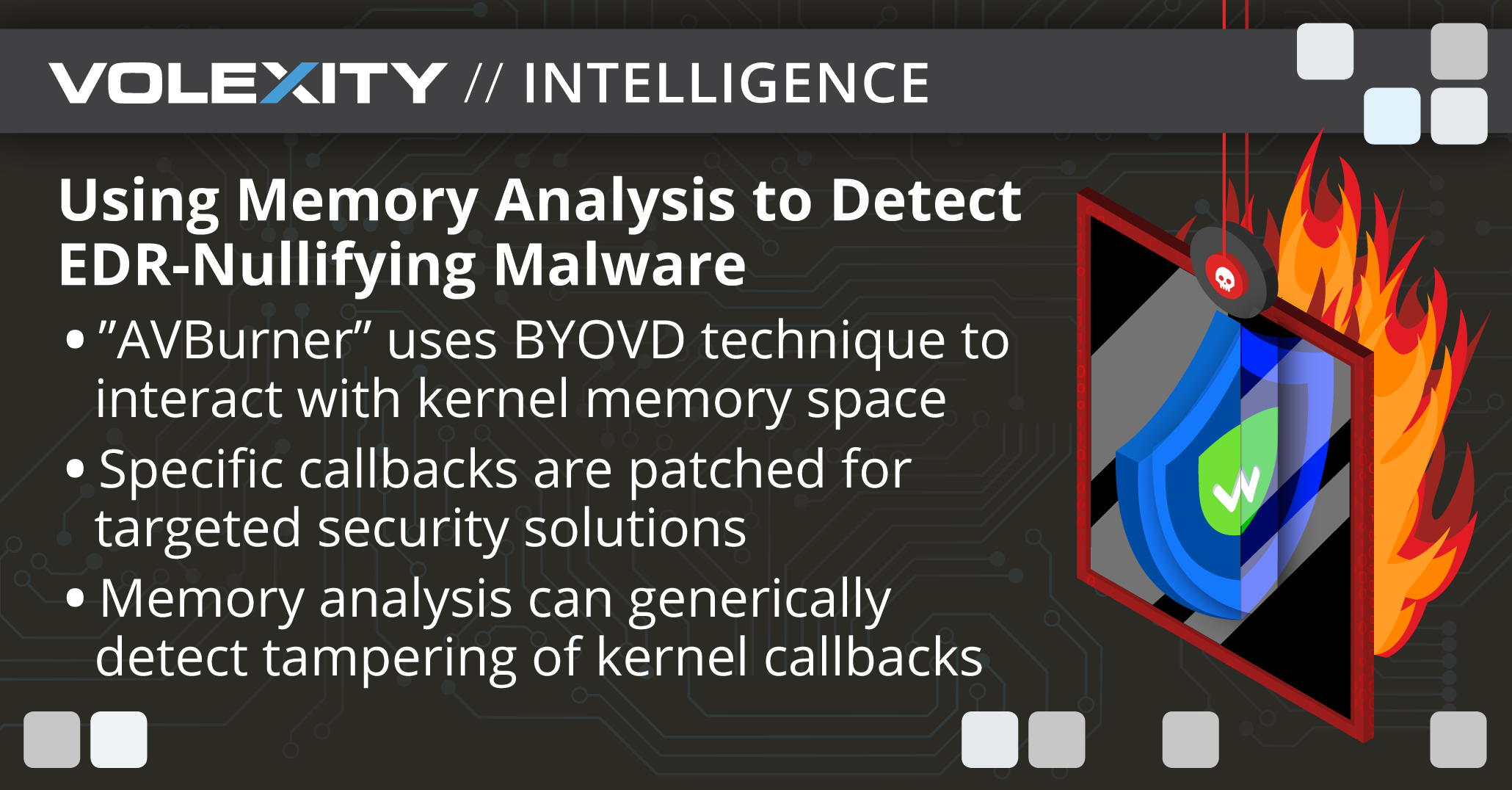
Using Memory Analysis to Detect EDR-Nullifying Malware

2016년 18주차 정보보안 뉴스클리핑

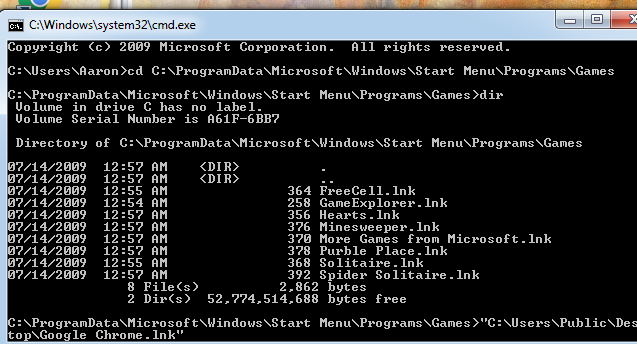
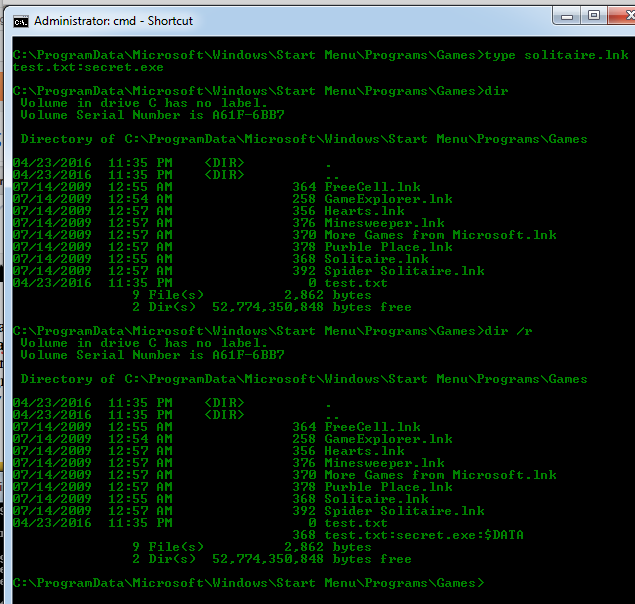
computer forensics:Initial Response & Volatile Data Collection from Windows system
DigitalResidue's Forensics
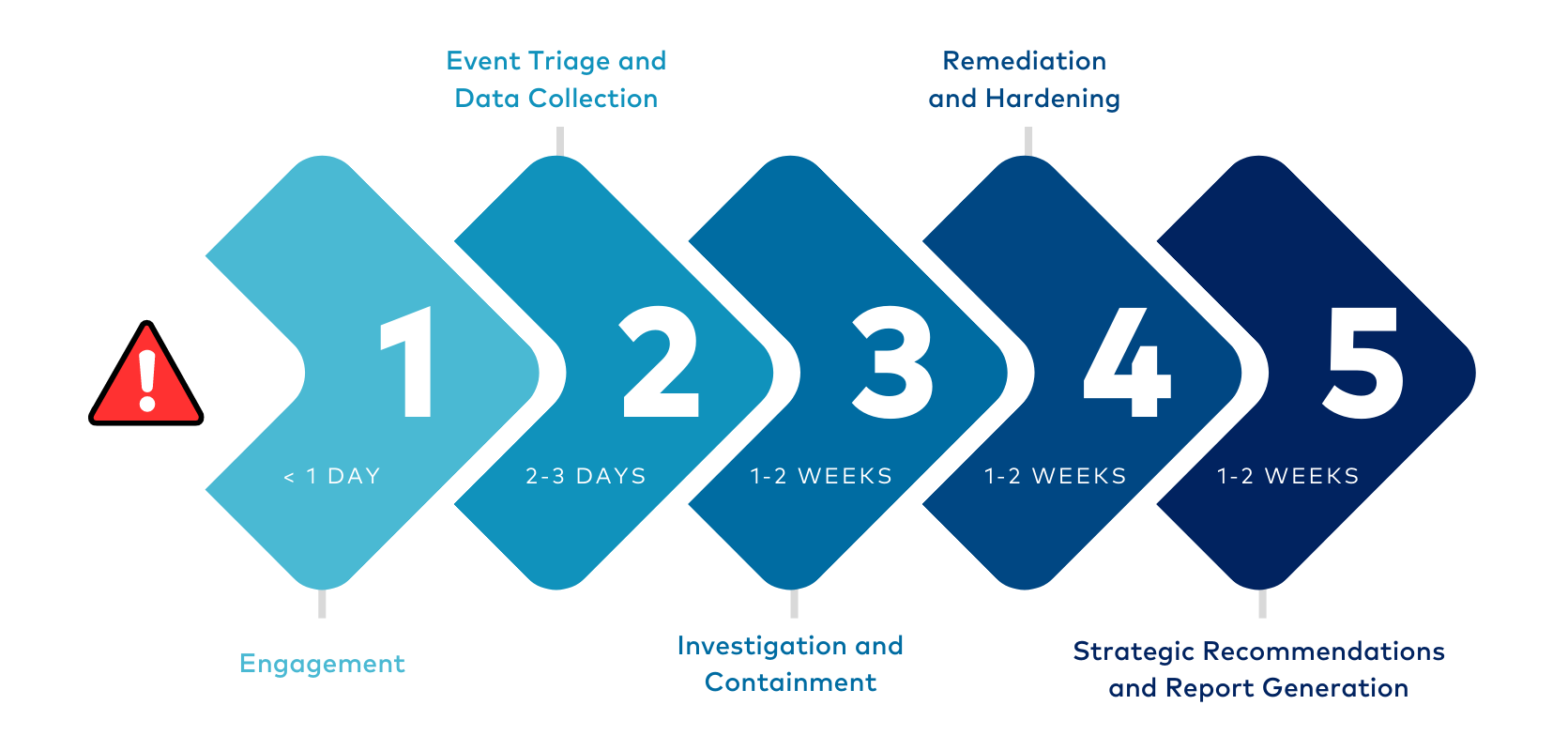
Digital Forensics and Incident Response (DFIR)

Distributed forensics and incident response in the enterprise - ScienceDirect

Distributed forensics and incident response in the enterprise - ScienceDirect
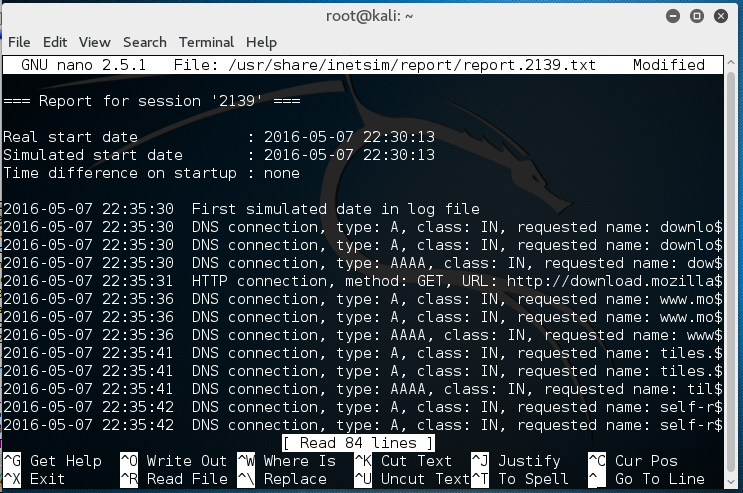
DigitalResidue's Forensics
Recomendado para você
-
Get Spider Solitaire Collection Free - Microsoft Store26 março 2025
-
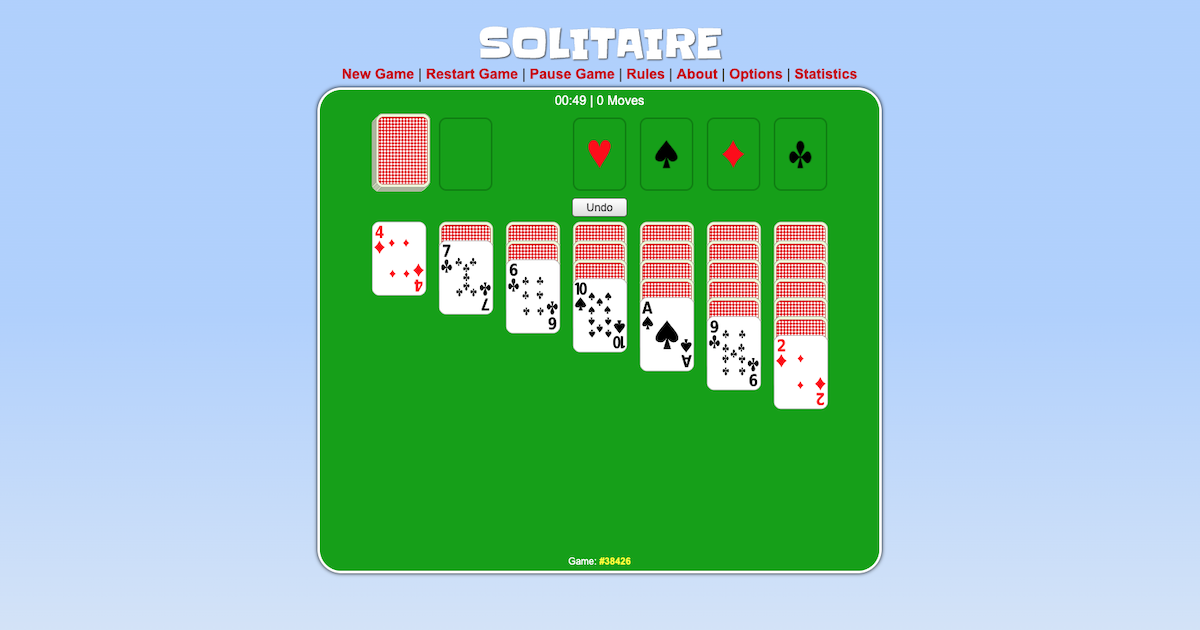 Solitaire Play it online26 março 2025
Solitaire Play it online26 março 2025 -
Solitaire Honda (@solitairehonda) • Instagram photos and videos26 março 2025
-
 Solitaire Showtime - Jam City26 março 2025
Solitaire Showtime - Jam City26 março 2025 -
 Palm Point and Palm Isles in Palm City26 março 2025
Palm Point and Palm Isles in Palm City26 março 2025 -
 Solitaire on the App Store26 março 2025
Solitaire on the App Store26 março 2025 -
 Kit Heath Cèleste Astoria Snow Pavè Necklace – Smyth Jewelers26 março 2025
Kit Heath Cèleste Astoria Snow Pavè Necklace – Smyth Jewelers26 março 2025 -
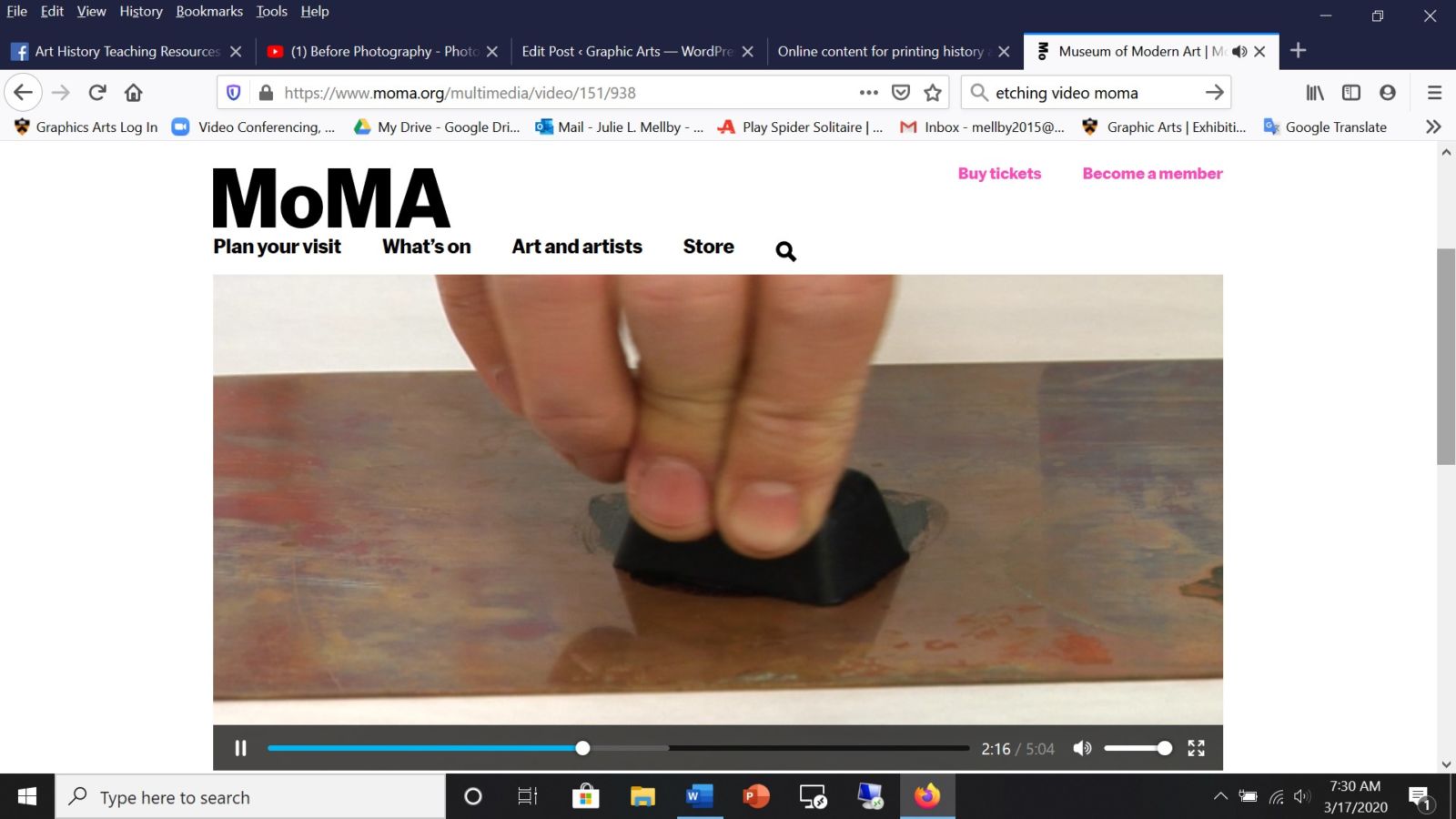 Online content for printing history and art history26 março 2025
Online content for printing history and art history26 março 2025 -
![🎮 How to PLAY [ Solitaire Grand Harvest ] on PC ▷ DOWNLOAD and INSTALL](https://i.ytimg.com/vi/q-FkXDpowII/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLCQvnkDRZ64GcDa0_j7N3RO3ckOyw) 🎮 How to PLAY [ Solitaire Grand Harvest ] on PC ▷ DOWNLOAD and INSTALL26 março 2025
🎮 How to PLAY [ Solitaire Grand Harvest ] on PC ▷ DOWNLOAD and INSTALL26 março 2025 -
 Top 10 Fixes for Google Drive Not Syncing Issues26 março 2025
Top 10 Fixes for Google Drive Not Syncing Issues26 março 2025
você pode gostar
-
 Urban Chaos: Riot Response (USA) PS2 ISO - CDRomance26 março 2025
Urban Chaos: Riot Response (USA) PS2 ISO - CDRomance26 março 2025 -
 One Piece Chapter 1034 – Sanji VS Queen: Germa Science26 março 2025
One Piece Chapter 1034 – Sanji VS Queen: Germa Science26 março 2025 -
 Von Regium (vonregium) - Profile26 março 2025
Von Regium (vonregium) - Profile26 março 2025 -
 Editora JBC lança o one-shot Fairy Tail Zero - Editora JBC26 março 2025
Editora JBC lança o one-shot Fairy Tail Zero - Editora JBC26 março 2025 -
 Golden hamster, Diet, Habitat & Lifespan26 março 2025
Golden hamster, Diet, Habitat & Lifespan26 março 2025 -
 The Last of Us Sales Surged in January on PS4 & PS526 março 2025
The Last of Us Sales Surged in January on PS4 & PS526 março 2025 -
 Saiba quem é Bia Haddad Maia, campeã no WTA Finals Elite, na China26 março 2025
Saiba quem é Bia Haddad Maia, campeã no WTA Finals Elite, na China26 março 2025 -
 HEQUSIGNS Live On Air Neon Signs, Live On Air LED Light Neon Sign26 março 2025
HEQUSIGNS Live On Air Neon Signs, Live On Air LED Light Neon Sign26 março 2025 -
Novo emote do Piseiro no Free Fire em 2023! 😍😂💚 #freefire #ffclub #26 março 2025
-
 HD desktop wallpaper: Overwatch, Video Game, Tracer (Overwatch26 março 2025
HD desktop wallpaper: Overwatch, Video Game, Tracer (Overwatch26 março 2025


