Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Last updated 01 abril 2025

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.

TeamCity Intrusion Saga: APT29 Suspected Among the Attackers Exploiting CVE-2023-42793
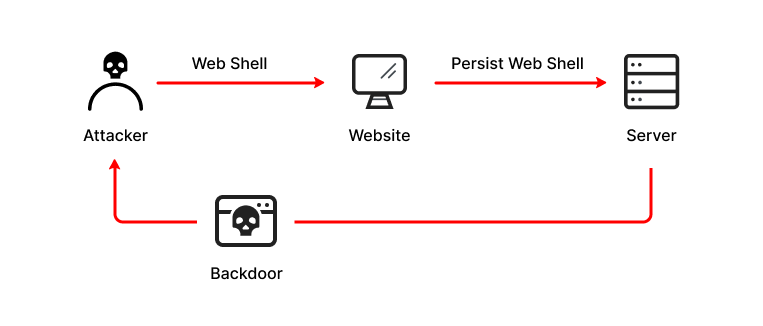
What is a Web Shell, Attack Types, Detection & Protection
Windows Defense Evasion Techniques
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
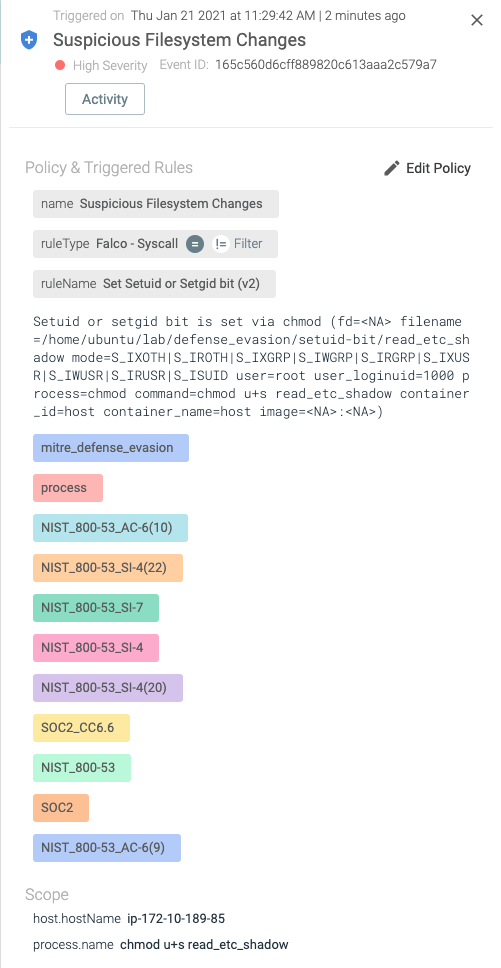
Detecting MITRE ATT&CK: Defense evasion techniques with Falco

Detecting MITRE ATT&CK: Defense evasion techniques with Falco
The Evolution of Malicious Shell Scripts

Linux Red Team Defense Evasion - Apache2 Rootkit

A sophisticated SkidMap variant targets unsecured Redis servers

Backtrack 5: Linux & Mac Systems Vulnerable to Malicious Scripts Too – CYBER ARMS – Computer Security
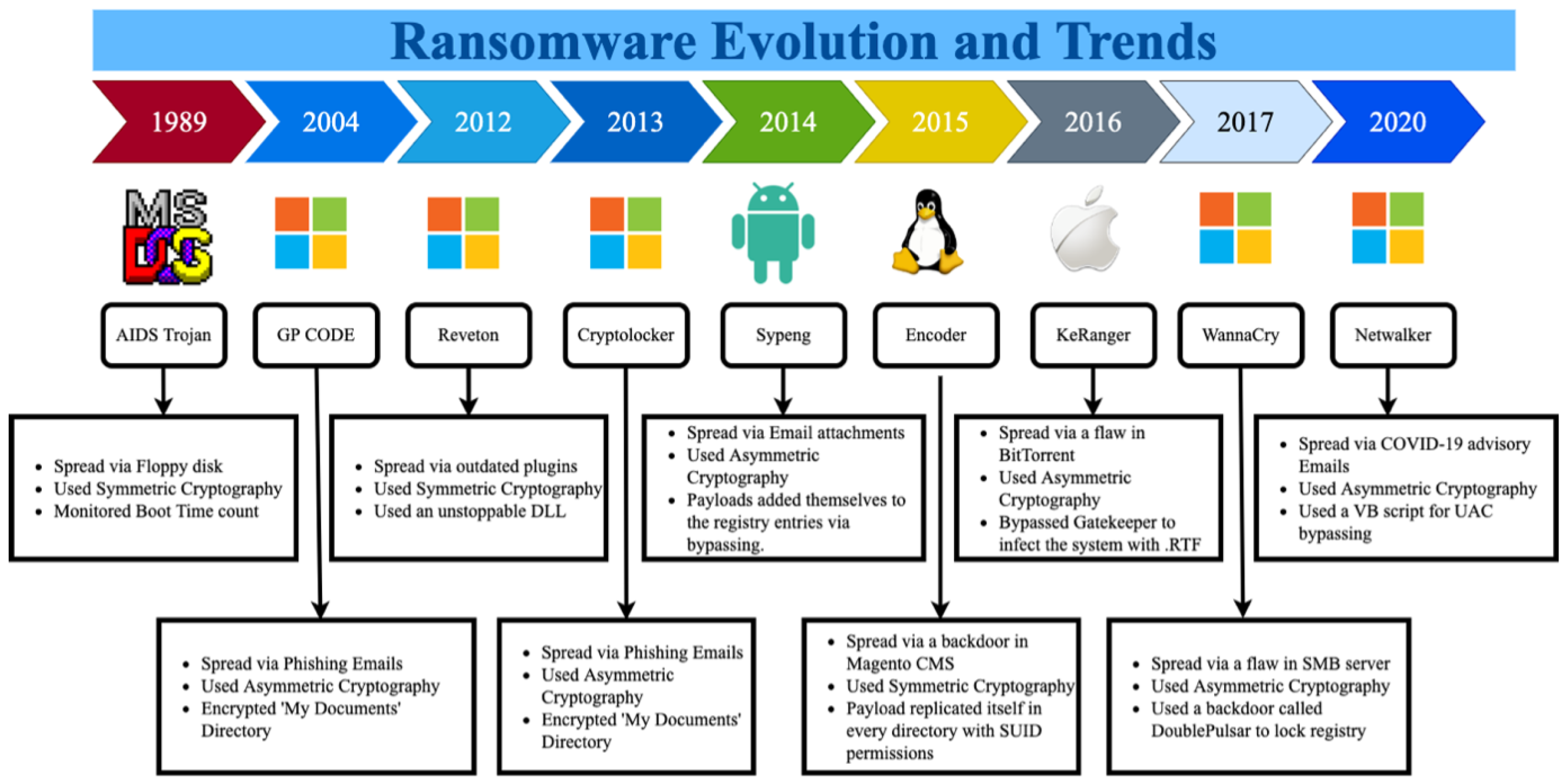
Sustainability, Free Full-Text
Recomendado para você
-
Evade Script Pastebin 202301 abril 2025
-
 BEST Roblox Evade Script GUI ESP Exploit Unpatched (2023 Pastebin01 abril 2025
BEST Roblox Evade Script GUI ESP Exploit Unpatched (2023 Pastebin01 abril 2025 -
 Evade Script/GUI Review01 abril 2025
Evade Script/GUI Review01 abril 2025 -
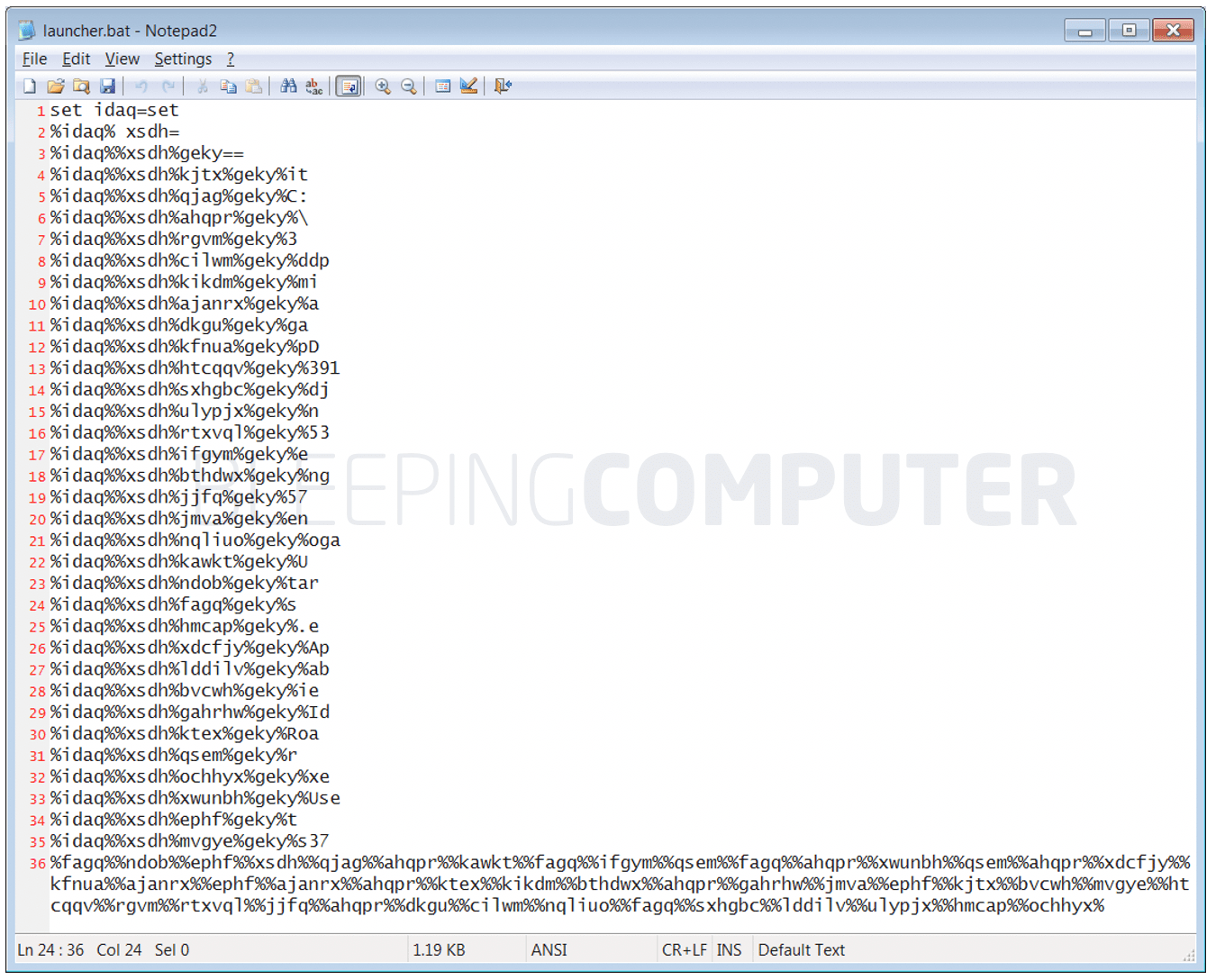 TrickBot malware uses obfuscated Windows batch script to evade01 abril 2025
TrickBot malware uses obfuscated Windows batch script to evade01 abril 2025 -
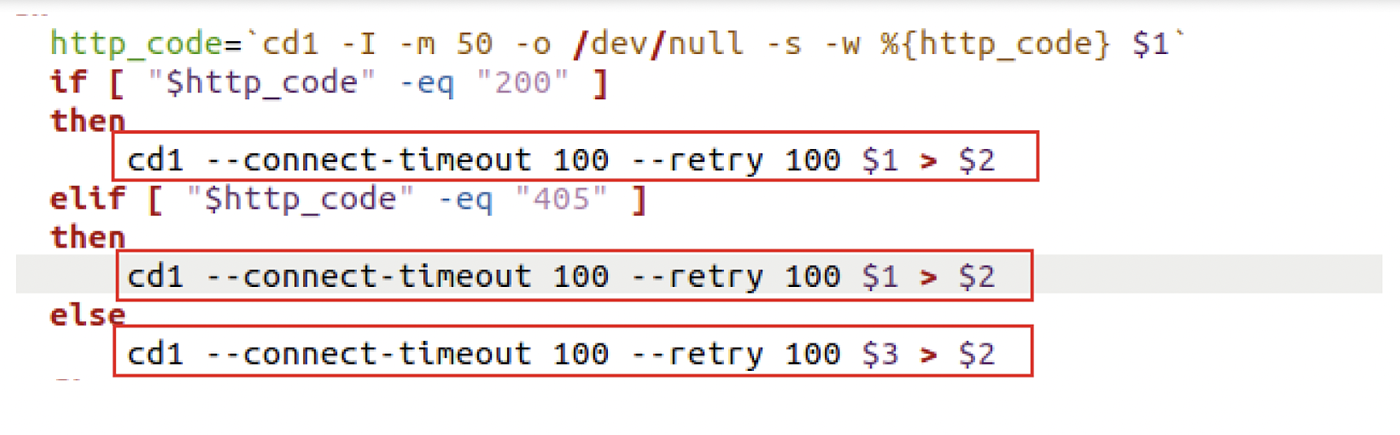
 Snippet of Server-side script generated by ChatGPT to evade01 abril 2025
Snippet of Server-side script generated by ChatGPT to evade01 abril 2025 -
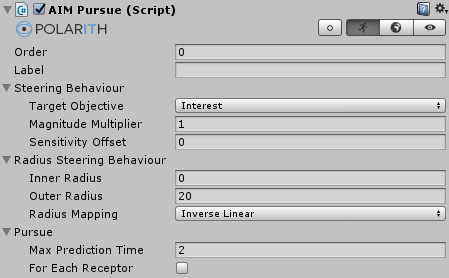 Polarith AI: Pursue and Evade01 abril 2025
Polarith AI: Pursue and Evade01 abril 2025 -
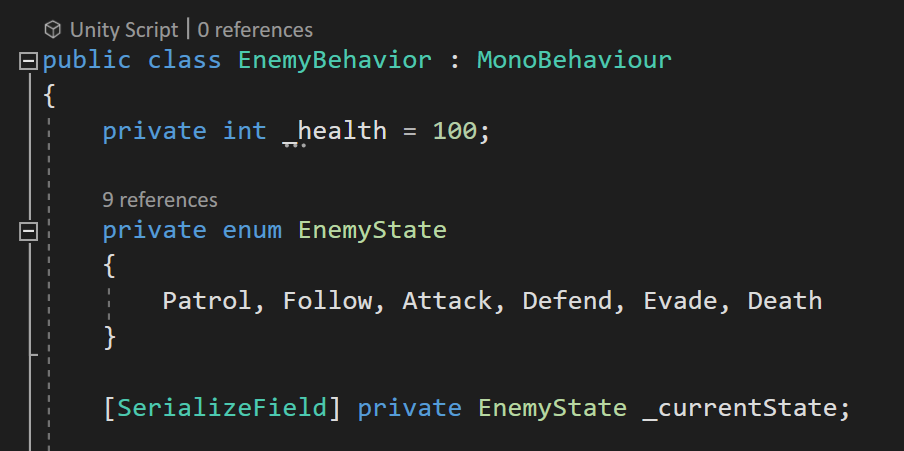 Enums. Using enums are a really useful way to…01 abril 2025
Enums. Using enums are a really useful way to…01 abril 2025 -
 Darkrai X Evade Script01 abril 2025
Darkrai X Evade Script01 abril 2025 -
 Analyzing Ruby malware - VMRay01 abril 2025
Analyzing Ruby malware - VMRay01 abril 2025 -
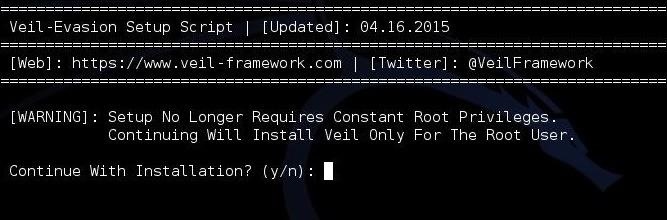 Hack Like a Pro: How to Evade AV Detection with Veil-Evasion01 abril 2025
Hack Like a Pro: How to Evade AV Detection with Veil-Evasion01 abril 2025
você pode gostar
-
 Hello Kitty para colorir em 2023 Hello kitty, Desenhos da hello kitty para colorir, Desenho da hello kitty01 abril 2025
Hello Kitty para colorir em 2023 Hello kitty, Desenhos da hello kitty para colorir, Desenho da hello kitty01 abril 2025 -
 Pequenos Grandes Pensantes.: Poesia O Macaco - Ruth Rocha01 abril 2025
Pequenos Grandes Pensantes.: Poesia O Macaco - Ruth Rocha01 abril 2025 -
 Monkey D. Luffy Manga anime one piece, One piece manga, Luffy01 abril 2025
Monkey D. Luffy Manga anime one piece, One piece manga, Luffy01 abril 2025 -
 Fã cria cosplay baseado em Luffy no país de Wano e o resultado é01 abril 2025
Fã cria cosplay baseado em Luffy no país de Wano e o resultado é01 abril 2025 -
 Eu amo a Sui! Ninguém pode contestar isso!😏(Rikei ga Koi ni Ochita no de Shoumei shitemita. Heart)01 abril 2025
Eu amo a Sui! Ninguém pode contestar isso!😏(Rikei ga Koi ni Ochita no de Shoumei shitemita. Heart)01 abril 2025 -
Video Games with Multiple Endings Part 2 #fyp #gaming #ps5 #videogames01 abril 2025
-
 Will we see mid-generation console refreshes again?01 abril 2025
Will we see mid-generation console refreshes again?01 abril 2025 -
 Royal Match: King's Nightmare Full Compilation - Save The King From Danger!!01 abril 2025
Royal Match: King's Nightmare Full Compilation - Save The King From Danger!!01 abril 2025 -
 Papel de Parede Vichy Cinza Claro - B Decor - Decoração para Casa e Quarto Infantil01 abril 2025
Papel de Parede Vichy Cinza Claro - B Decor - Decoração para Casa e Quarto Infantil01 abril 2025 -
Penguin Diner 2 — play online for free on Yandex Games01 abril 2025