Malware analysis Malicious activity
Por um escritor misterioso
Last updated 30 março 2025

Malware Analysis: Steps & Examples - CrowdStrike

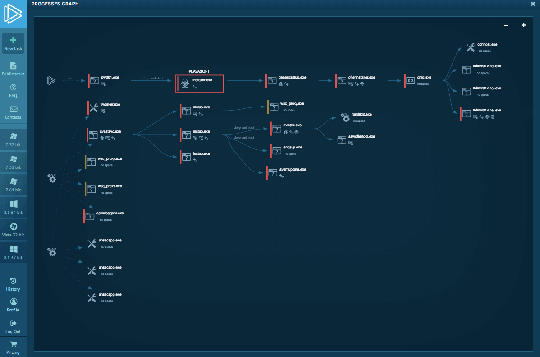
Playbook of the Week: Malware Investigation and Response - Palo Alto Networks Blog

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs
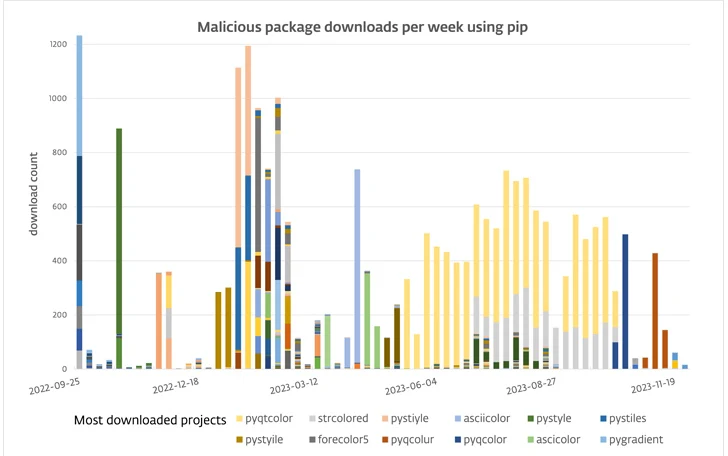
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems

Mastering Malware Analysis
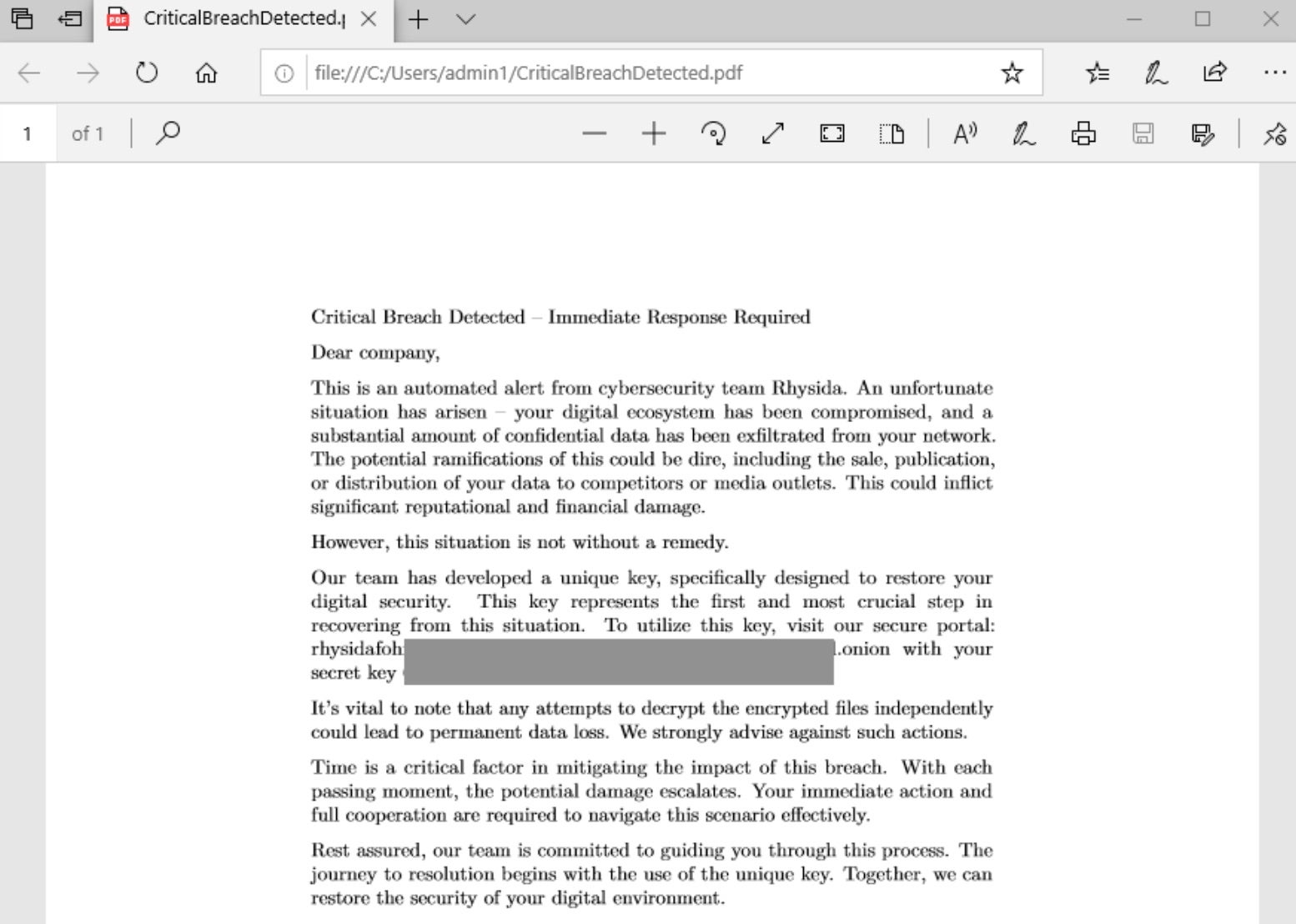
Rhysida - SentinelOne

Feature Extraction and Detection of Malwares Using Machine Learning

Interactive Online Malware Sandbox

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

How to build a malware analysis sandbox with Elastic Security

Remediation and Malware Detection Overview

Malware analysis AIO_4.9.8__ed.rar Malicious activity
Interactive Online Malware Sandbox

Playbook for Malware outbreak
Recomendado para você
-
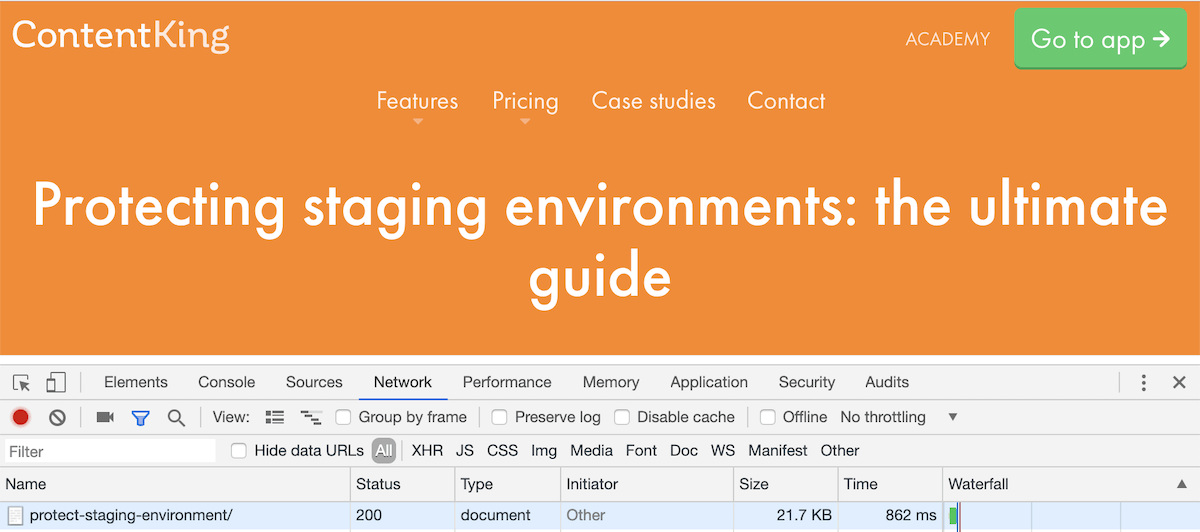
 429 Error – Too Many Requests HTTP Code Explained30 março 2025
429 Error – Too Many Requests HTTP Code Explained30 março 2025 -
 How To Fix HTTP Error 429: Cause And Fixes - MiniTool30 março 2025
How To Fix HTTP Error 429: Cause And Fixes - MiniTool30 março 2025 -
 How to Fix the HTTP 429 Too Many Requests Error30 março 2025
How to Fix the HTTP 429 Too Many Requests Error30 março 2025 -
 What would cause HTTP ERROR 429 but only for search results? : r/Searx30 março 2025
What would cause HTTP ERROR 429 but only for search results? : r/Searx30 março 2025 -
 Four Ways To Fix Error 429: Too Many Requests30 março 2025
Four Ways To Fix Error 429: Too Many Requests30 março 2025 -
 how to solve status code 429 on hitting an instagram api with axios - Stack Overflow30 março 2025
how to solve status code 429 on hitting an instagram api with axios - Stack Overflow30 março 2025 -
 We're sorry but you have sent too many requests to us recently Google30 março 2025
We're sorry but you have sent too many requests to us recently Google30 março 2025 -
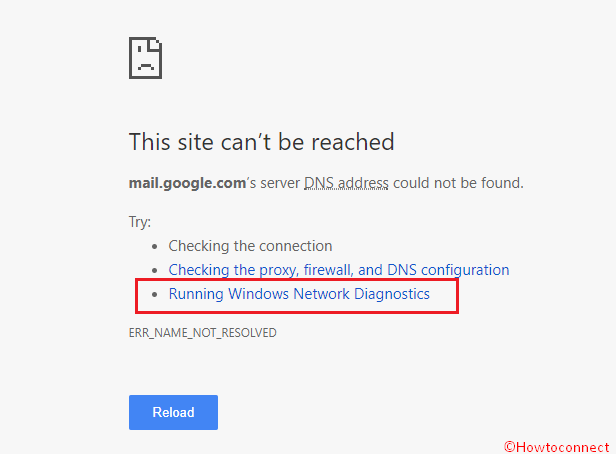 How to Fix Error 429 in Chrome Browser30 março 2025
How to Fix Error 429 in Chrome Browser30 março 2025 -
How to Fix Error 429?30 março 2025
-
 cdn.sanity.io/images/tkl0o0xu/production/6772195c530 março 2025
cdn.sanity.io/images/tkl0o0xu/production/6772195c530 março 2025
você pode gostar
-
 Polus.gg Steam Charts · SteamDB30 março 2025
Polus.gg Steam Charts · SteamDB30 março 2025 -
 Batman Arkham City Lockdown developer NetherRealm would30 março 2025
Batman Arkham City Lockdown developer NetherRealm would30 março 2025 -
 Mario Kart Tournament at Ponderosa Joint-Use Branch Tickets, Sat30 março 2025
Mario Kart Tournament at Ponderosa Joint-Use Branch Tickets, Sat30 março 2025 -
 Fun Blox Fairy Land Girls Collection Swan Castle Blocks, Multi30 março 2025
Fun Blox Fairy Land Girls Collection Swan Castle Blocks, Multi30 março 2025 -
 Quackity Skin for Paper Craft Minecraft Skin30 março 2025
Quackity Skin for Paper Craft Minecraft Skin30 março 2025 -
 Os 20 melhores jogos de PSP para quem gosta do portátil! - Liga30 março 2025
Os 20 melhores jogos de PSP para quem gosta do portátil! - Liga30 março 2025 -
 ALL NEW *FREE POINTS* UPDATE CODES in FUNKY FRIDAY CODES! (Funky Friday Codes) ROBLOX30 março 2025
ALL NEW *FREE POINTS* UPDATE CODES in FUNKY FRIDAY CODES! (Funky Friday Codes) ROBLOX30 março 2025 -
 How to conduct conversion analysis - Voxco30 março 2025
How to conduct conversion analysis - Voxco30 março 2025 -
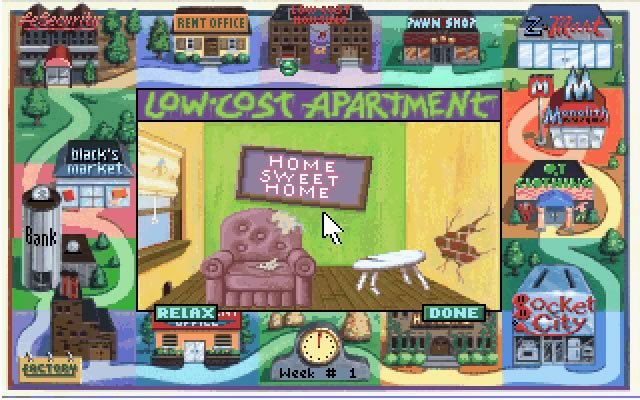 Jones in the Fast Lane: board game meets life simulation - Abandonware DOS30 março 2025
Jones in the Fast Lane: board game meets life simulation - Abandonware DOS30 março 2025 -
 Alphabet Lore But Fixing Letters - The letter F but it is Amongus30 março 2025
Alphabet Lore But Fixing Letters - The letter F but it is Amongus30 março 2025
