Malware analysis Malicious activity
Por um escritor misterioso
Last updated 30 março 2025

Malware analysis metasploit.bat Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Cybersecurity Search Engine

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Malware analysis Program_Install_and_Uninstall Malicious activity

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
TryHackMe Hacktivities

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs

Malware analysis index.html Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
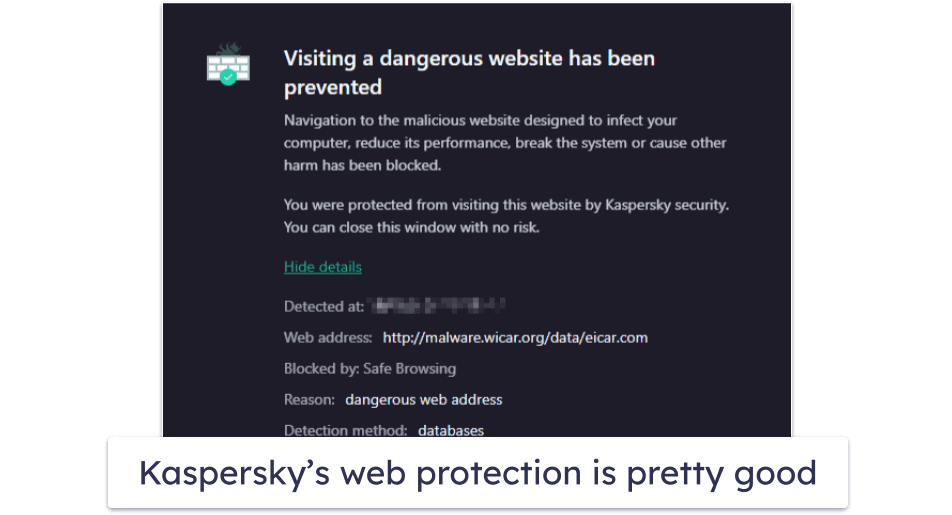
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
Recomendado para você
-
.jpg) FL Studio Producer Edition Portable Windows 7-8.1-10 - 64 Bit (All30 março 2025
FL Studio Producer Edition Portable Windows 7-8.1-10 - 64 Bit (All30 março 2025 -
Cute Pixelated Corgi #7 - PIXELATED CORGIS30 março 2025
-
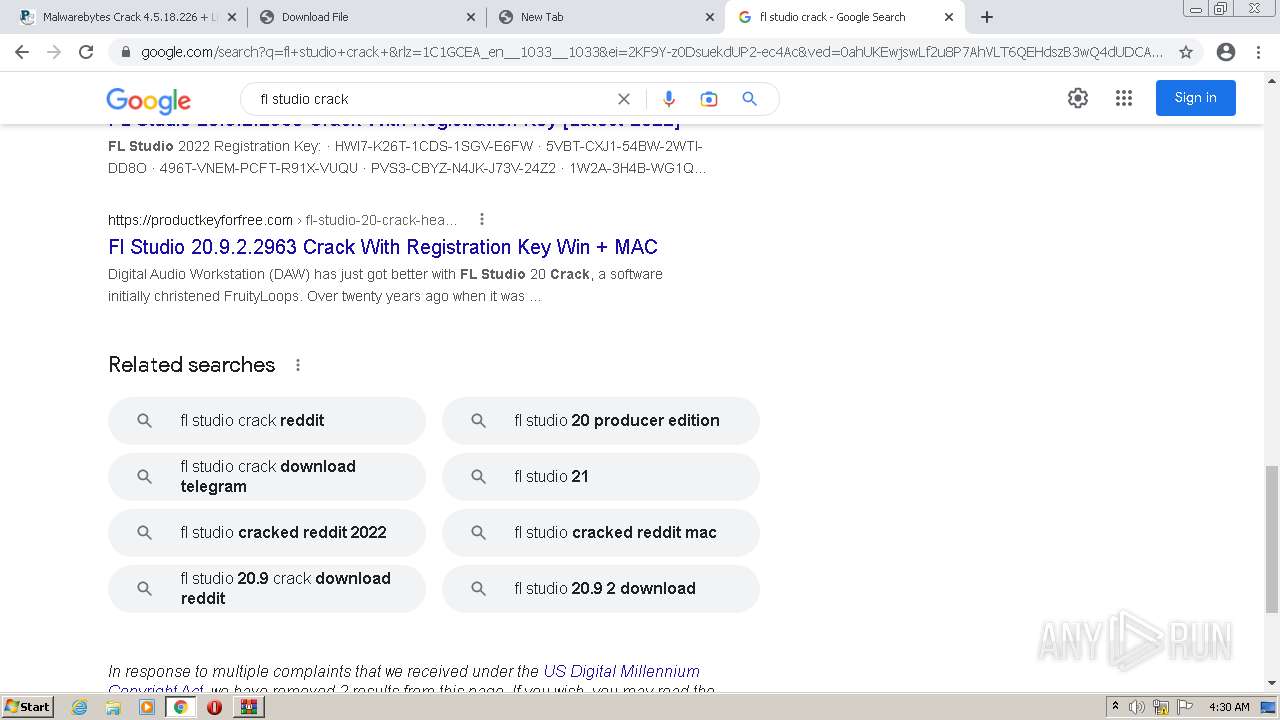
 Fl studio 20 cracked : r/CrackedSoftware_CZ30 março 2025
Fl studio 20 cracked : r/CrackedSoftware_CZ30 março 2025 -
 The Cheapest Way to Buy FL Studio: Where to buy a key at a low price30 março 2025
The Cheapest Way to Buy FL Studio: Where to buy a key at a low price30 março 2025 -
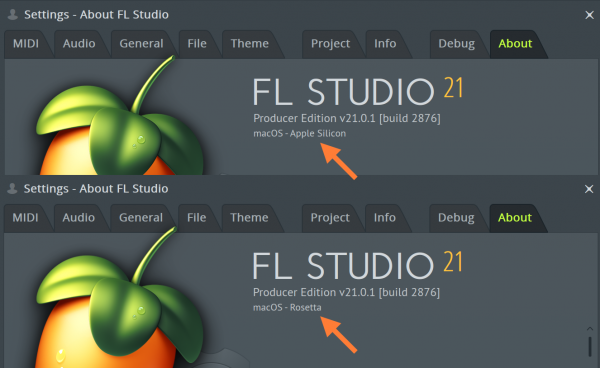 FL Studio Apple Silicon ARM Processors - M1 & M2 Support. FL Studio macOS / OSX.30 março 2025
FL Studio Apple Silicon ARM Processors - M1 & M2 Support. FL Studio macOS / OSX.30 março 2025 -
Why is the song sound low volume when exported in FL studio? - Quora30 março 2025
-
 cracked fl studio virus|TikTok Search30 março 2025
cracked fl studio virus|TikTok Search30 março 2025 -
 anyone have a good FL studio crack? : r/VocaTorrent30 março 2025
anyone have a good FL studio crack? : r/VocaTorrent30 março 2025 -
 How Surreal Cereal's Fake Celebrity Campaign Took the Marketing World by Storm30 março 2025
How Surreal Cereal's Fake Celebrity Campaign Took the Marketing World by Storm30 março 2025 -
Inclusion of Hydrophobic Liquids in Silica Aerogel Microparticles in an Aqueous Process: Microencapsulation and Extra Pore Creation30 março 2025
você pode gostar
-
Terraria Soundtrack, Scott Lloyd Shelly30 março 2025
-
 Giving Away Robux in PLS DONATE, Roblox30 março 2025
Giving Away Robux in PLS DONATE, Roblox30 março 2025 -
 Stumble Guys Mod Apk Download Dinheiro Infinito v0.61 - Goku Play Games30 março 2025
Stumble Guys Mod Apk Download Dinheiro Infinito v0.61 - Goku Play Games30 março 2025 -
 2.0 Pro Plus Land Carving Surf Skate 25x82cm Surfing Simulation30 março 2025
2.0 Pro Plus Land Carving Surf Skate 25x82cm Surfing Simulation30 março 2025 -
 Buster Scruggs30 março 2025
Buster Scruggs30 março 2025 -
 Rumor: Far Cry 7 Will Come as a Day-One Launch on Nintendo30 março 2025
Rumor: Far Cry 7 Will Come as a Day-One Launch on Nintendo30 março 2025 -
 Noir Stardia, The Hidden Dungeon Only I Can Enter Wiki30 março 2025
Noir Stardia, The Hidden Dungeon Only I Can Enter Wiki30 março 2025 -
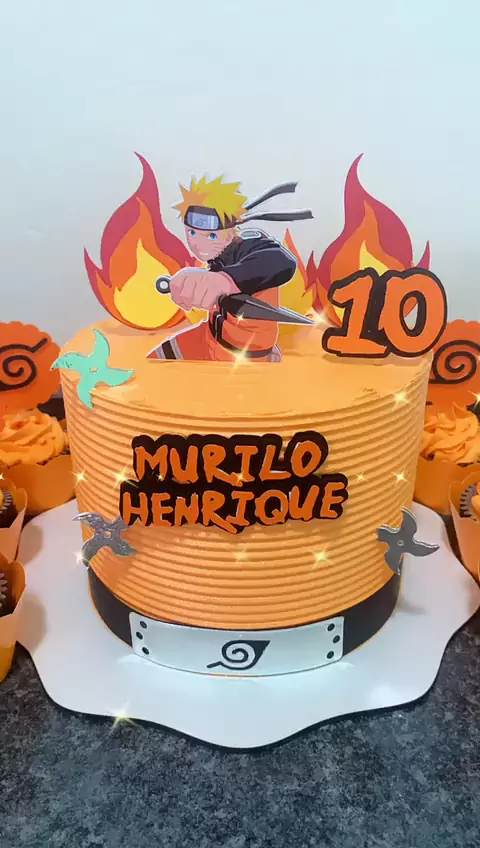 topo de bolo naruto feminino30 março 2025
topo de bolo naruto feminino30 março 2025 -
 Fly Or Die: Jogue Fly Or Die gratuitamente em LittleGames30 março 2025
Fly Or Die: Jogue Fly Or Die gratuitamente em LittleGames30 março 2025 -
 PLATOON (1986) – Movie Valhalla30 março 2025
PLATOON (1986) – Movie Valhalla30 março 2025

