Indirect Command Execution – Penetration Testing Lab
Por um escritor misterioso
Last updated 06 abril 2025

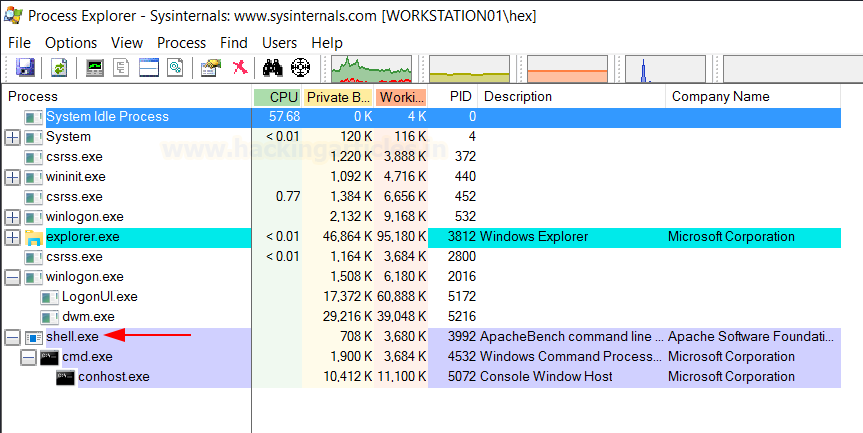
The windows ecosystem provides multiple binaries that could be used by adversaries to execute arbitrary commands that will evade detection especially in environments that are monitoring binaries such as "cmd.exe". In certain occasions the techniques described below could be used to bypass application whitelisting products if rules are not configured properly (whitelist by path or…

TryHackMe Hacktivities

Indirect Command Execution – Penetration Testing Lab

Indirect Command Execution – Penetration Testing Lab
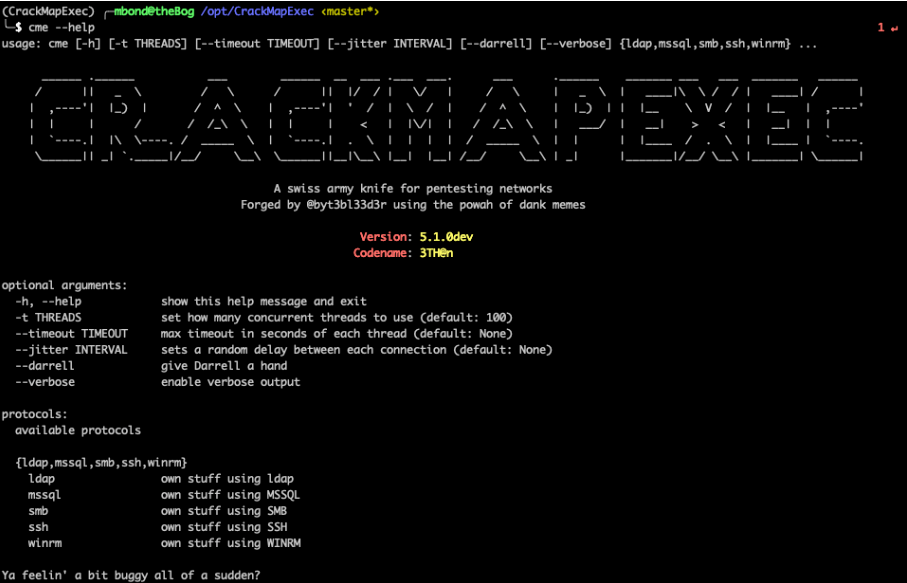
CrackMapExec Basics. One of the tools that I like to use…, by Mike Bond
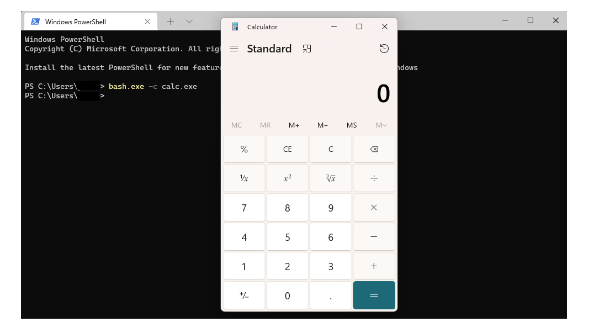
TRY HACK ME: Living Off The Land Write-Up, by Shefali Kumari

TryHackMe Hacktivities

command execution walkthrough – Penetration Testing Lab
Offensive Security Training - Applied Technology Academy

Premium Lab Walkthrough: Command Injection, by Pentester Academy
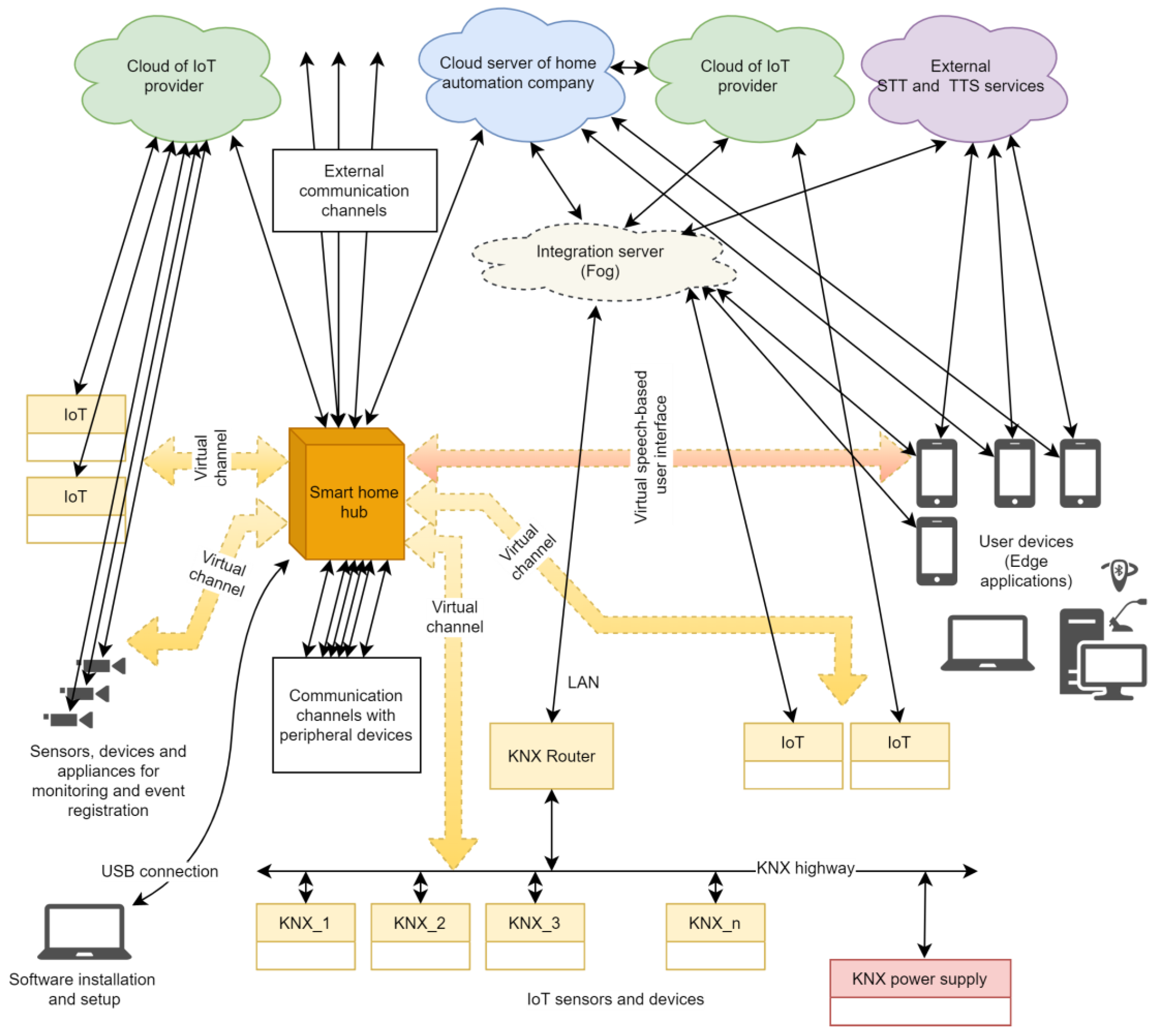
Electronics, Free Full-Text
Indirect Command Execution: Defense Evasion (T1202) - Hacking Articles
Recomendado para você
-
 administrator - Force cmd.exe prompt to run NOT as admin - Super User06 abril 2025
administrator - Force cmd.exe prompt to run NOT as admin - Super User06 abril 2025 -
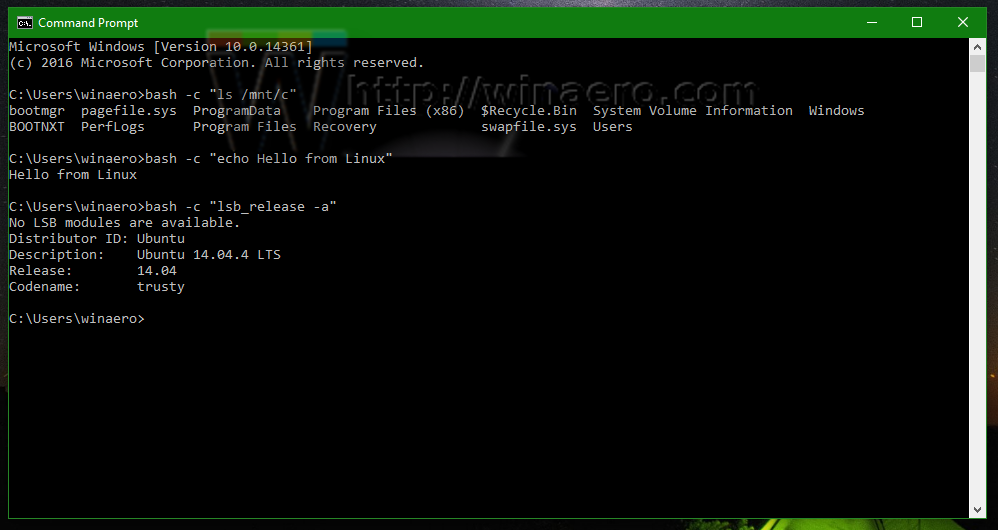 Run Linux commands from cmd.exe prompt in Windows 1006 abril 2025
Run Linux commands from cmd.exe prompt in Windows 1006 abril 2025 -
 How to Run an EXE File at the Command Prompt in 8 Easy Steps06 abril 2025
How to Run an EXE File at the Command Prompt in 8 Easy Steps06 abril 2025 -
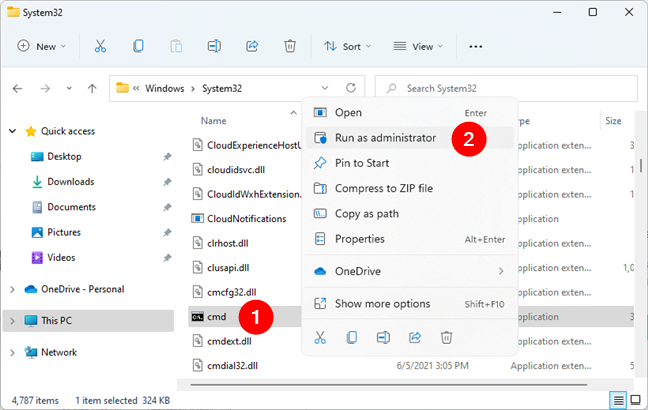 How to open Command Prompt (14 ways) - Digital Citizen06 abril 2025
How to open Command Prompt (14 ways) - Digital Citizen06 abril 2025 -
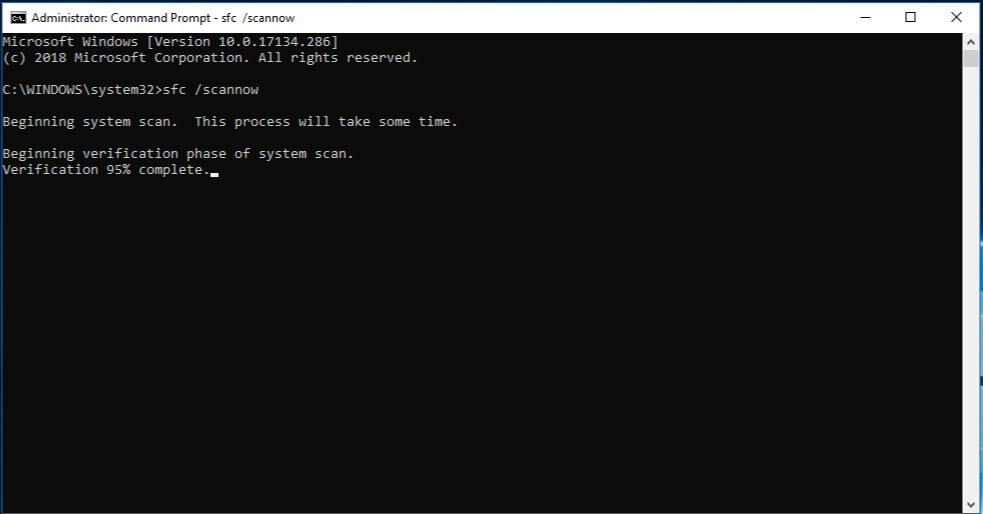 Use the System File Checker tool to repair missing or corrupted06 abril 2025
Use the System File Checker tool to repair missing or corrupted06 abril 2025 -
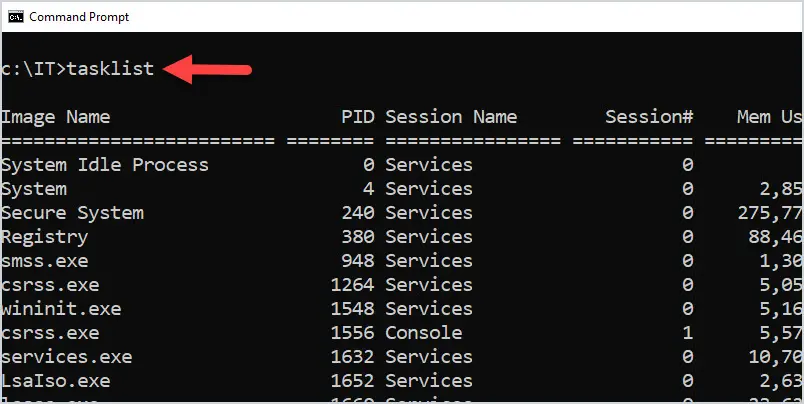 50 Basic Windows Commands with Examples - Active Directory Pro06 abril 2025
50 Basic Windows Commands with Examples - Active Directory Pro06 abril 2025 -
Run exe or shell command without cmd window popup · Issue #249 · espanso/espanso · GitHub06 abril 2025
-
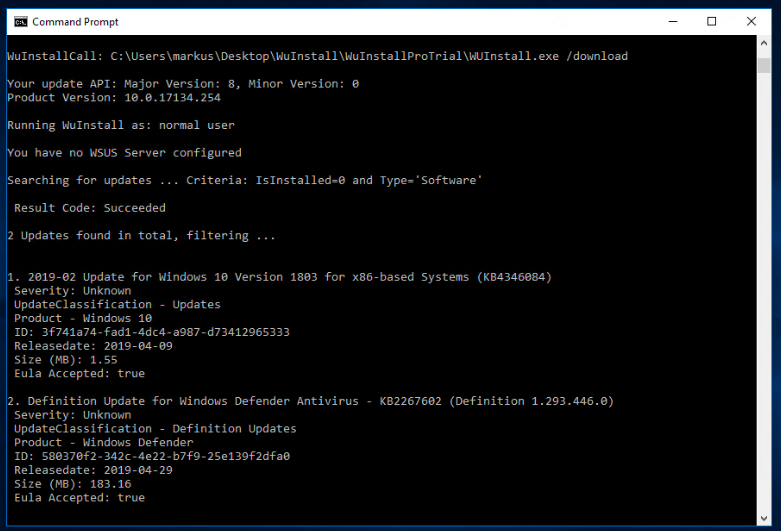 WuInstall - How to force Windows 10 updates to install using the command line06 abril 2025
WuInstall - How to force Windows 10 updates to install using the command line06 abril 2025 -
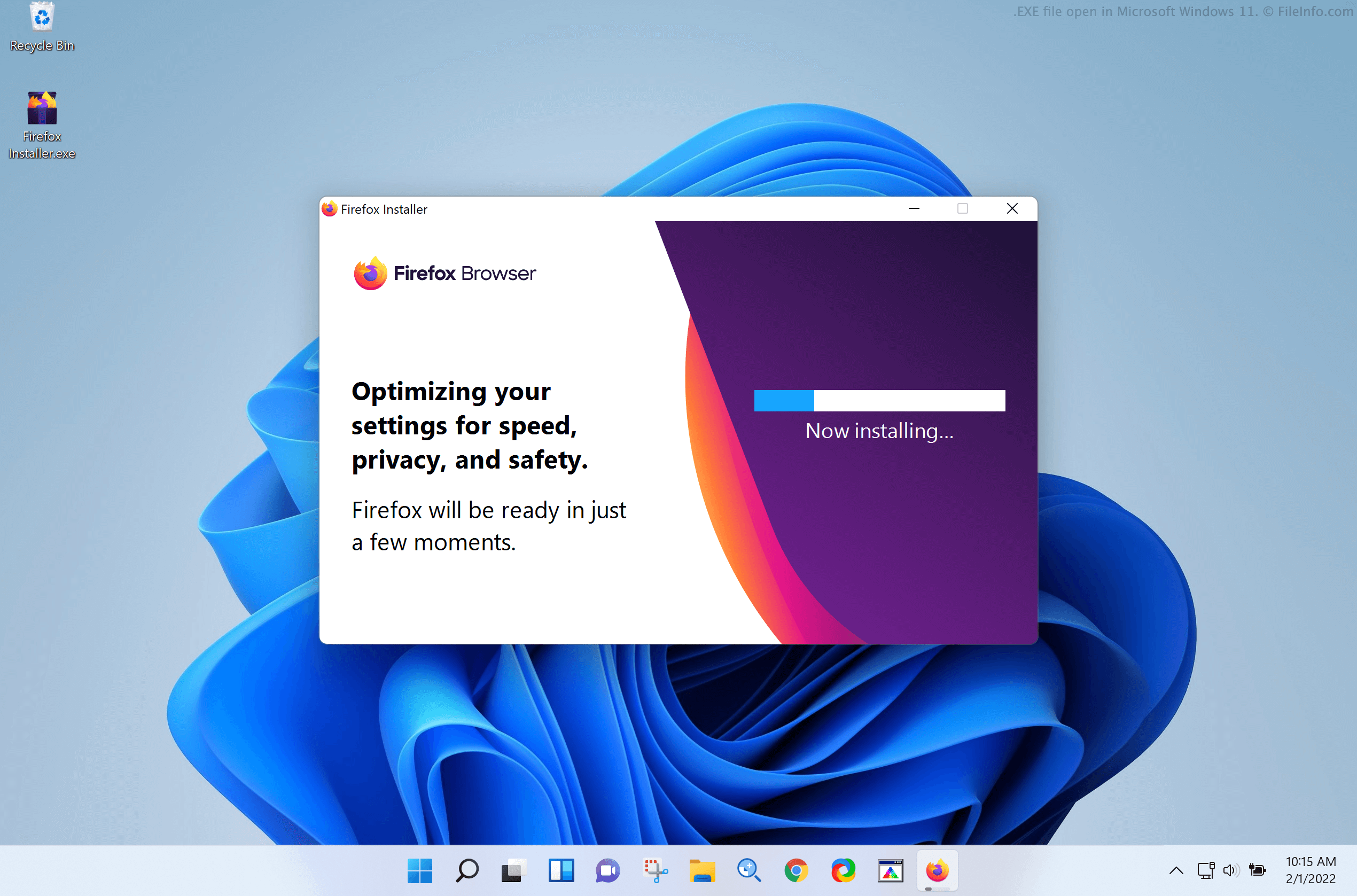 EXE File - What is an .exe file and how do I open it?06 abril 2025
EXE File - What is an .exe file and how do I open it?06 abril 2025 -
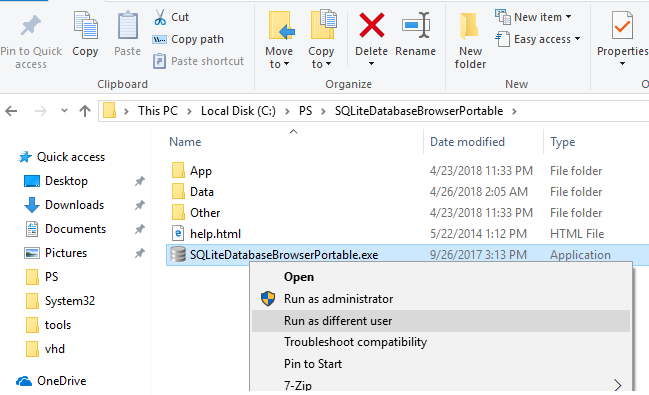 How to Run a Program as a Different User (RunAs) in Windows06 abril 2025
How to Run a Program as a Different User (RunAs) in Windows06 abril 2025
você pode gostar
-
 aula 5 de ingles Lily lean english06 abril 2025
aula 5 de ingles Lily lean english06 abril 2025 -
 Eleição para o Conselho Tutelar: servidor, candidate-se - SISMUC06 abril 2025
Eleição para o Conselho Tutelar: servidor, candidate-se - SISMUC06 abril 2025 -
 How do I launch a program from command line without opening a new cmd window? - Stack Overflow06 abril 2025
How do I launch a program from command line without opening a new cmd window? - Stack Overflow06 abril 2025 -
 The Rock SUS Sound06 abril 2025
The Rock SUS Sound06 abril 2025 -
![Tabuleiro de Xadrez Madeira Brava excelente acabamento 54x54cm casas 5.6cm Espessura 13mm [Sob Encomenda: Envio em 25 dias]](https://cdn.awsli.com.br/600x450/1805/1805746/produto/190415973/8f60262ec0.jpg) Tabuleiro de Xadrez Madeira Brava excelente acabamento 54x54cm casas 5.6cm Espessura 13mm [Sob Encomenda: Envio em 25 dias]06 abril 2025
Tabuleiro de Xadrez Madeira Brava excelente acabamento 54x54cm casas 5.6cm Espessura 13mm [Sob Encomenda: Envio em 25 dias]06 abril 2025 -
 vempra_jagoodlooks, J.A Good Looks06 abril 2025
vempra_jagoodlooks, J.A Good Looks06 abril 2025 -
 goofy ahh ohio sound effects by Arkhalsi06 abril 2025
goofy ahh ohio sound effects by Arkhalsi06 abril 2025 -
Outriders: Day One Edition - Xbox One/series X : Target06 abril 2025
-
 O HARÉM DE SETSU SUZUKI EM ISEKAI SHOUKAN WA NIDOME DESU06 abril 2025
O HARÉM DE SETSU SUZUKI EM ISEKAI SHOUKAN WA NIDOME DESU06 abril 2025 -
Koruveda - ¿Qué es Ananda? 🍃🌀 #ChangingHabits #Koruveda #CremaDentalNatural #CepilloDeBambu #BambooToothBrush #PazMental06 abril 2025