Advanced Apple Debugging & Reverse Engineering, Chapter 31
Por um escritor misterioso
Last updated 08 abril 2025

In this chapter, you'll use DTrace to hook objc_msgSend's entry probe and pull out the class name along with the Objective-C selector for that class. By the end of this chapter, you'll have LLDB generating a DTrace script which only generates tracing info for code implemented within the main executable that calls objc_msgSend.
Used Book in Good Condition Highlight, take notes, and search in the book

Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and Obfuscation

Access Our Reverse Engineering

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started

Kodeco Learn iOS, Android & Flutter

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started

Advanced Apple Debugging & Reverse Engineering (3rd Edition) - 2018

Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace vs. objc_msgSend

Mastering Malware Analysis
Reverse Engineering UIKit to Fix Our Top Crash
Apple Debugging L8 - Reverse Engineering Basics
Recomendado para você
-
Flee The Facility Scripts08 abril 2025
-
BuxBack - Earn R$08 abril 2025
-
Fer99908 abril 2025
-
como canjear en rbx gum|Búsqueda de TikTok08 abril 2025
-
 crisairys gacha gachafer (cgachafer) - Profile08 abril 2025
crisairys gacha gachafer (cgachafer) - Profile08 abril 2025 -
 WR DRESSMAKERS RECEIVE CAPACITY BUILDING FROM TTU's IDCE, CTVET - Takoradi Technical University08 abril 2025
WR DRESSMAKERS RECEIVE CAPACITY BUILDING FROM TTU's IDCE, CTVET - Takoradi Technical University08 abril 2025 -
 Discuss Everything About Bubble Gum Simulator Wiki08 abril 2025
Discuss Everything About Bubble Gum Simulator Wiki08 abril 2025 -
 RPS_Leaks - Pet Simulator Leaks☁️ on X: New Pets Cat Ruby, Monkey Emerald ,Dragon Amethyst , Corgi Mystic View Thread (2) for a better view of the pets #PetSimulatorX /08 abril 2025
RPS_Leaks - Pet Simulator Leaks☁️ on X: New Pets Cat Ruby, Monkey Emerald ,Dragon Amethyst , Corgi Mystic View Thread (2) for a better view of the pets #PetSimulatorX /08 abril 2025 -
easy rbx|TikTok Search08 abril 2025
-
 Seed Junky Home08 abril 2025
Seed Junky Home08 abril 2025
você pode gostar
-
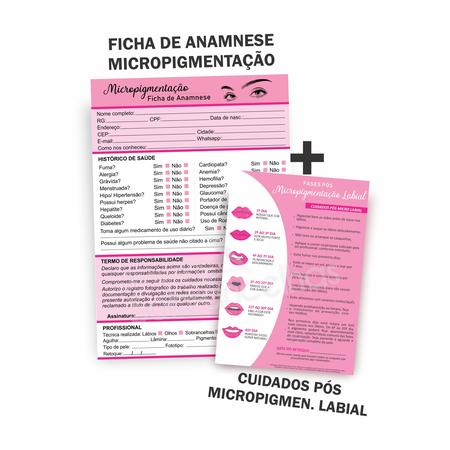 Kit Ficha Anamnese Labial + Cuidados Cliente A Mais Completa - SDS08 abril 2025
Kit Ficha Anamnese Labial + Cuidados Cliente A Mais Completa - SDS08 abril 2025 -
 The Outlast Trials Breaks Sales Records: Impressive Revenue and08 abril 2025
The Outlast Trials Breaks Sales Records: Impressive Revenue and08 abril 2025 -
 Alphabet lore plushies : r/alphabetfriends08 abril 2025
Alphabet lore plushies : r/alphabetfriends08 abril 2025 -
 PDF) Relato De Experiência: Wordwall Como Ferramenta De Gamificação No Ensino Remoto08 abril 2025
PDF) Relato De Experiência: Wordwall Como Ferramenta De Gamificação No Ensino Remoto08 abril 2025 -
 Crazy Light - PrimeTime Amusements08 abril 2025
Crazy Light - PrimeTime Amusements08 abril 2025 -
Classroom of the Elite S02 EP1008 abril 2025
-
 The power of failure: making 'The Last of Us08 abril 2025
The power of failure: making 'The Last of Us08 abril 2025 -
 Learn To Fish - All-Waters08 abril 2025
Learn To Fish - All-Waters08 abril 2025 -
 SCP Foundation - a poem by Ted Alexander - All Poetry08 abril 2025
SCP Foundation - a poem by Ted Alexander - All Poetry08 abril 2025 -
 desenho de árvore de natal 4429724 Vetor no Vecteezy08 abril 2025
desenho de árvore de natal 4429724 Vetor no Vecteezy08 abril 2025


